- 02 March 2026 (1 messages)
-

- 03 March 2026 (1 messages)
-
 Joined.
Joined. - 05 March 2026 (8 messages)
-
 [discord] <kolie> o/ having issues with hyberdbg, watchdog timeout, critical structure corruption, hypervade define being inverted logic from what it should, !hide not working at all .
[discord] <kolie> o/ having issues with hyberdbg, watchdog timeout, critical structure corruption, hypervade define being inverted logic from what it should, !hide not working at all . -
 [discord] <kolie> Not sure where to start, but I'd be willing to debug/test/contribute to get it working.
[discord] <kolie> Not sure where to start, but I'd be willing to debug/test/contribute to get it working. -
 [discord] <kolie> Got an app I'm trying to work with and as soon as I start it, the machine locks up. Sometimes when I load vmm I get lockup / watchdog blue screen.
[discord] <kolie> Got an app I'm trying to work with and as soon as I start it, the machine locks up. Sometimes when I load vmm I get lockup / watchdog blue screen. -
 [discord] <kolie> I was hoping maybe something in hyperevade helped with the lockup.
[discord] <kolie> I was hoping maybe something in hyperevade helped with the lockup. -
 [discord] <kolie> !hide just basically says it can't work as soon as I try to load it.
[discord] <kolie> !hide just basically says it can't work as soon as I try to load it. -
 [discord] <kolie> !hide itself doesn't seem to work, it seems its global anyways I guess, when I looked at the code, even if I give it a pid, its enabled for everything, but I don't even get that far ( I'm fine if its global, just curious observations ).
[discord] <kolie> !hide itself doesn't seem to work, it seems its global anyways I guess, when I looked at the code, even if I give it a pid, its enabled for everything, but I don't even get that far ( I'm fine if its global, just curious observations ). -
 [discord] <kolie> I got transparent debugging enabled by taking out the logging null checks.
[discord] <kolie> I got transparent debugging enabled by taking out the logging null checks. -
 [discord] <kolie> Got a watchdog timeout as soon as I started the program I want to work with.
[discord] <kolie> Got a watchdog timeout as soon as I started the program I want to work with. - 06 March 2026 (3 messages)
-

-
 [discord] <unrustled.jimmies> [reply]: critical structure corruption seems like kpp/patchguard. did you disable it?
[discord] <unrustled.jimmies> [reply]: critical structure corruption seems like kpp/patchguard. did you disable it? -
 [discord] <kolie> Yea patchguard off.
[discord] <kolie> Yea patchguard off. - 07 March 2026 (1 messages)
-
 [discord] <unrustled.jimmies> can you upload the minidump?
[discord] <unrustled.jimmies> can you upload the minidump? - 08 March 2026 (2 messages)
-
 [discord] <kolie> Not sure if it produces ill check
[discord] <kolie> Not sure if it produces ill check -

- 09 March 2026 (1 messages)
-

- 13 March 2026 (1 messages)
-
Joined.
- 14 March 2026 (2 messages)
-
 [discord] <__writecr4> used hyperdbg as a vital reference for this project here: https://github.com/zer0condition/Ophion
[discord] <__writecr4> used hyperdbg as a vital reference for this project here: https://github.com/zer0condition/Ophion
seen some people asking if anyone has isolated just the hv from the hyperdbg project so going to drop it here, hope they find it helpfulGitHub - zer0condition/Ophion: Stealth-focused Intel VT-x hypervisor (EAC/BE/ACs/AVs).Stealth-focused Intel VT-x hypervisor (EAC/BE/ACs/AVs). - zer0condition/Ophion
-
Joined.
- 15 March 2026 (2 messages)
-
 [discord] <rayanfam> [reply]: Interesting. Thanks for sharing
[discord] <rayanfam> [reply]: Interesting. Thanks for sharing -
 [discord] <rayanfam> This is also an interesting analysis, seems that they directly used HyperDbg in their project:
[discord] <rayanfam> This is also an interesting analysis, seems that they directly used HyperDbg in their project:
https://github.com/RD945/hypervisor-crack-auditGitHub - RD945/hypervisor-crack-audit: Security analysis of the hypervisor drm method used to bypass denuvo. Reverse engineering of the driver loaders and boot components using GhidraSecurity analysis of the hypervisor drm method used to bypass denuvo. Reverse engineering of the driver loaders and boot components using Ghidra - RD945/hypervisor-crack-audit
- 18 March 2026 (2 messages)
-
 Joined.
Joined. -
Joined.
- 19 March 2026 (21 messages)
-

-
 What?
What? -
 You dont see the git link>
You dont see the git link> -
 This one?
This one? -

-
 I didn't download it, just read the markdown file.
I didn't download it, just read the markdown file. -
 But thanks for informing us about it 👍
But thanks for informing us about it 👍 -
 [discord] <zer0condition> [reply]: i don’t think you understand that this is an article/blog post which is about reverse engineering a certain cracking method used in Denuvo-protected games, also the person who posted it is a lead developer/founding member of HyperDbg
[discord] <zer0condition> [reply]: i don’t think you understand that this is an article/blog post which is about reverse engineering a certain cracking method used in Denuvo-protected games, also the person who posted it is a lead developer/founding member of HyperDbg -
 I just read it. I didn't download anything. The work itself was really good.
I just read it. I didn't download anything. The work itself was really good. -
 The only mistake (in case of HyperDbg) that I noticed was this one:
The only mistake (in case of HyperDbg) that I noticed was this one: -
 Right now, we just support VMX, not SVM.
Right now, we just support VMX, not SVM. -
 [discord] <zer0condition> [reply]: yep i havent read up on it personally, its not mine, the project posted above it (Ophion) is
[discord] <zer0condition> [reply]: yep i havent read up on it personally, its not mine, the project posted above it (Ophion) is -
 I think he meant this file, not Ophion:
I think he meant this file, not Ophion: -
 But again, I don't know, I didn't download anything.
But again, I don't know, I didn't download anything. -
 [discord] <zer0condition> yep got it, i was just clarifying because he seemed to have misunderstood what rayanfam had posted
[discord] <zer0condition> yep got it, i was just clarifying because he seemed to have misunderstood what rayanfam had posted -
 BTW, I also checked Ophion, it was really an impressive project.
BTW, I also checked Ophion, it was really an impressive project. -
 Yes, that's also my discord account.
Yes, that's also my discord account. -
 [discord] <zer0condition> appreciate the kind works, it still has alot of potential and future work to be put into
[discord] <zer0condition> appreciate the kind works, it still has alot of potential and future work to be put into -
 [discord] <zer0condition> words*
[discord] <zer0condition> words* -
 Also, FYI we have a project called HyperEvade (which is currently disabled because anti viruses flag it as malicious probably because of certain string), but in case if you were interested, feel free to add codes there. Or maybe we could also add some of your codes to HyperDbg in the future.
Also, FYI we have a project called HyperEvade (which is currently disabled because anti viruses flag it as malicious probably because of certain string), but in case if you were interested, feel free to add codes there. Or maybe we could also add some of your codes to HyperDbg in the future. -
 and yes, that's certainly a broad area of research and development. Nice work. 👍
and yes, that's certainly a broad area of research and development. Nice work. 👍 - 20 March 2026 (105 messages)
-
 Can you explain in detail, if is possible, what to turn off before starting hyperdbg, because I turned off a lot things but still complained about something
Can you explain in detail, if is possible, what to turn off before starting hyperdbg, because I turned off a lot things but still complained about something -
Joined.
-
-
 I saw it intercepting only the next call of rdtsc to bypass time-based detections, won't this be detected easily by calling rdtsc twice or by adding some other instructions before calling rdtsc
I saw it intercepting only the next call of rdtsc to bypass time-based detections, won't this be detected easily by calling rdtsc twice or by adding some other instructions before calling rdtsc -
RDTSC timing countermeasure
-
Is this tool already included?
-
 Hey,
Hey,
I was preparing an Intel Core Ultra 2xx for HyperDbg and it seems there are a lot of things changed there. There is also device guard that needs to be disabled to disable VBS so it took us a bit of time to run HyperDbg but we finally made it. Are you running on Core Ultra 2XX processor? -
 Or is it a different processor/problem?
Or is it a different processor/problem? -
 [discord] <zer0condition> [reply]: the classic pattern is rdtsc -> cpuid -> rdtsc, that's what hvdetecc, VMAware, and anti-cheats actually run, trapping the next RDTSC defeats it with zero perf cost
[discord] <zer0condition> [reply]: the classic pattern is rdtsc -> cpuid -> rdtsc, that's what hvdetecc, VMAware, and anti-cheats actually run, trapping the next RDTSC defeats it with zero perf cost -
 [discord] <zer0condition> trapping every RDTSC unconditionally is a non-starter, TSC reads happen constantly (spinlocks, scheduler, profiling), the perf hit itself becomes a detection vector
[discord] <zer0condition> trapping every RDTSC unconditionally is a non-starter, TSC reads happen constantly (spinlocks, scheduler, profiling), the perf hit itself becomes a detection vector -
 [discord] <zer0condition> double RDTSC after CPUID? first gets compensated, second gets raw, but youd need to know the expected delta on bare metal which varies by CPU/microcode/P-state, statistical attack that needs a baseline
[discord] <zer0condition> double RDTSC after CPUID? first gets compensated, second gets raw, but youd need to know the expected delta on bare metal which varies by CPU/microcode/P-state, statistical attack that needs a baseline -
 [discord] <zer0condition> adding nops or other instructions? the trap disarms on any intervening exit (interrupt, NMI, etc), not just RDTSC, on a live system with interrupts firing constantly, more instructions = higher chance something else disarms it
[discord] <zer0condition> adding nops or other instructions? the trap disarms on any intervening exit (interrupt, NMI, etc), not just RDTSC, on a live system with interrupts firing constantly, more instructions = higher chance something else disarms it -
 [discord] <zer0condition> detector cant tell the difference
[discord] <zer0condition> detector cant tell the difference -
 [discord] <zer0condition> but nobodys running these attacks in practice afaik, current approach passes everything tested
[discord] <zer0condition> but nobodys running these attacks in practice afaik, current approach passes everything tested -
 [discord] <zer0condition> [reply]: yes, that among other things, most detection mechanisms employed by anti-cheats, anti-malware, etc, are to be covered, currently EAC is the main testing environment since it has one of the most strict hypervisor detection mechanisms for commercial products and it passes it
[discord] <zer0condition> [reply]: yes, that among other things, most detection mechanisms employed by anti-cheats, anti-malware, etc, are to be covered, currently EAC is the main testing environment since it has one of the most strict hypervisor detection mechanisms for commercial products and it passes it -
 [discord] <zer0condition> Hyperion by Byfron technologies also have interesting mechanisms from what ive heard, will be looking at that next
[discord] <zer0condition> Hyperion by Byfron technologies also have interesting mechanisms from what ive heard, will be looking at that next -
 I was wondering how making VBS mandatory on newer systems (enabled by default) affects projects that attempt to detect hypervisors using general techniques like RDTSC or CPUID. Are these general mitigation (e.g., RDTSC/CPUID) methods still significant in malware and anti cheats?
I was wondering how making VBS mandatory on newer systems (enabled by default) affects projects that attempt to detect hypervisors using general techniques like RDTSC or CPUID. Are these general mitigation (e.g., RDTSC/CPUID) methods still significant in malware and anti cheats? -
 Because if there is a VBS running inside a machine then by default we should expect RDTSC/CPUID.
Because if there is a VBS running inside a machine then by default we should expect RDTSC/CPUID. -
 [discord] <zer0condition> [reply]: VBS on by default changes the baseline, theres always a hypervisor now, so the usual "detect any hypervisor" becomes useless, every modern Windows box would trigger it
[discord] <zer0condition> [reply]: VBS on by default changes the baseline, theres always a hypervisor now, so the usual "detect any hypervisor" becomes useless, every modern Windows box would trigger it -
 Exactly
Exactly -
 [discord] <zer0condition> detection shifts to finding a rogue hypervisor on top of Hyper-V, anti-cheats have to whitelist Hyper-V's signature and look for nested layers, or use hypercalls to verify it's actually microsoft's code, generic CPUID/RDTSC checks just detect VBS doing its job
[discord] <zer0condition> detection shifts to finding a rogue hypervisor on top of Hyper-V, anti-cheats have to whitelist Hyper-V's signature and look for nested layers, or use hypercalls to verify it's actually microsoft's code, generic CPUID/RDTSC checks just detect VBS doing its job -
 [discord] <zer0condition> still matters for non-VBS systems (gaming rigs with VBS off for performance) and nested scenarios hiding under Hyper-V
[discord] <zer0condition> still matters for non-VBS systems (gaming rigs with VBS off for performance) and nested scenarios hiding under Hyper-V -
 [discord] <zer0condition> but yeah, relevance shrinks as VBS adoption grows
[discord] <zer0condition> but yeah, relevance shrinks as VBS adoption grows -
 Yes, exactly. I think it's a big change for hypervisor detection methods.
Yes, exactly. I think it's a big change for hypervisor detection methods. -
 [discord] <zer0condition> for the malware stuff, its the same scenario i suppose? they need sandbox-specific artifacts instead
[discord] <zer0condition> for the malware stuff, its the same scenario i suppose? they need sandbox-specific artifacts instead -
 [discord] <zer0condition> but yeah there are alot of pay-2-cheats or projects that are already hooking the microsoft hypervisor before the windows even boots using a bootkit
[discord] <zer0condition> but yeah there are alot of pay-2-cheats or projects that are already hooking the microsoft hypervisor before the windows even boots using a bootkit -
 👍
👍 -
 [discord] <zer0condition> they have alot of stuff to detect anyone abusing the mshv for cheat purposes too
[discord] <zer0condition> they have alot of stuff to detect anyone abusing the mshv for cheat purposes too -
Joined.
-
 Which
Which -
 [discord] <zer0condition> [reply]: some old acquiantances of mine have made a really comprehensive write-up on deobfuscating a very popular provider recently which uses exactly that, here is the link to it if you'd like to readup: https://x.com/BackEngineerLab/status/2020030645616201731Back Engineering Labs (@BackEngineerLab) on X
[discord] <zer0condition> [reply]: some old acquiantances of mine have made a really comprehensive write-up on deobfuscating a very popular provider recently which uses exactly that, here is the link to it if you'd like to readup: https://x.com/BackEngineerLab/status/2020030645616201731Back Engineering Labs (@BackEngineerLab) on XWe’re releasing our analysis of https://t.co/y7UypbGS8Z, a major game cheat targeted by multiple studios in recent legal actions. We partially deobfuscated several Themida-protected components and document how it hijacks Hyper-V to inject and manipulate game code.
-
 Does Themida finally support kernel drivers?
Does Themida finally support kernel drivers? -
 Can't enter to link
Can't enter to link -
 Mostly Valorant cheats I assume
Mostly Valorant cheats I assume -
 [discord] <zer0condition> https://back.engineering/blog/04/02/2026/Deobfuscation and Analysis of Ring-1.io
[discord] <zer0condition> https://back.engineering/blog/04/02/2026/Deobfuscation and Analysis of Ring-1.ioAs part of this research, we partially deobfuscated multiple Themida-protected binaries used by ring-1.io, including its UEFI bootloader implant. Several critical functions were recovered to enable static analysis of the implant’s behavior. This work provides visibility into mechanisms that are intentionally designed to resist inspection, including virtualization-assisted hooks, execution redirection, and kernel manipulation techniques.
-
 [discord] <zer0condition> https://github.com/backengineering/ring-1.ioGitHub - backengineering/ring-1.io: Deobfuscation and Analysis of Ring-1.io
[discord] <zer0condition> https://github.com/backengineering/ring-1.ioGitHub - backengineering/ring-1.io: Deobfuscation and Analysis of Ring-1.ioDeobfuscation and Analysis of Ring-1.io. Contribute to backengineering/ring-1.io development by creating an account on GitHub.
-
 Ohh
Ohh -
 [discord] <zer0condition> [reply]: the main binary is a UEFI bootkit, and yes you can make it work with even UEFI modules, same with VMProtect, just a matter of switching the subsystem type and doing Virtualization + Mutation only
[discord] <zer0condition> [reply]: the main binary is a UEFI bootkit, and yes you can make it work with even UEFI modules, same with VMProtect, just a matter of switching the subsystem type and doing Virtualization + Mutation only -
 Vmprotect supports drivers but afaik themida didnt
Vmprotect supports drivers but afaik themida didnt -
 They said codevirtualizer supports it
They said codevirtualizer supports it -
 [discord] <zer0condition> i did not bother reading properly through it regarding this, you may, there are alot of things that are being done wrongly though.
[discord] <zer0condition> i did not bother reading properly through it regarding this, you may, there are alot of things that are being done wrongly though. -
 There are bin2bin obfuscators also
There are bin2bin obfuscators also -
 Everyone is making hypervisors nowadays
Everyone is making hypervisors nowadays -
 If this goes on piracy and cheating scene will turn into a big mess like Android rooting scene is
If this goes on piracy and cheating scene will turn into a big mess like Android rooting scene is -
 [discord] <zer0condition> hypervisors have always been in the cheating scene, just not too common, they are way ahead of warez and malware scene, most competent people i know of, have been reversing anti-cheats and deploying them for stealthy internals, since way before 2021.
[discord] <zer0condition> hypervisors have always been in the cheating scene, just not too common, they are way ahead of warez and malware scene, most competent people i know of, have been reversing anti-cheats and deploying them for stealthy internals, since way before 2021. -
 It's way more common today
It's way more common today -
 [discord] <zer0condition> yeah but your point? doesnt really help the fact that most of them don't do things properly and are caught before they can get it to run
[discord] <zer0condition> yeah but your point? doesnt really help the fact that most of them don't do things properly and are caught before they can get it to run -
 I think it's because of the Denuvo news
I think it's because of the Denuvo news -
 Sure. Most of them are poorly written
Sure. Most of them are poorly written -
 Yeah. Cs.rin.ru is literally standardizing hypervisors as we speak
Yeah. Cs.rin.ru is literally standardizing hypervisors as we speak -
 [discord] <zer0condition> [reply]: not really, that is a joke of a "crack", they are just adding more overhead for things that can be done without going to that extend, its overkill, ive reversed some binaries of it and saw nothing impressive except CPUID and KUSER_SHARED_DATA related spoofing, its just a overhyped hardware spoofer.
[discord] <zer0condition> [reply]: not really, that is a joke of a "crack", they are just adding more overhead for things that can be done without going to that extend, its overkill, ive reversed some binaries of it and saw nothing impressive except CPUID and KUSER_SHARED_DATA related spoofing, its just a overhyped hardware spoofer. -
 I've entered on this site, there are some news about CSGO
I've entered on this site, there are some news about CSGO -
 It's a steam underground forum
It's a steam underground forum -
 Lmao
Lmao -
 Why is it on Russian
Why is it on Russian -
 Forum is Russia based
Forum is Russia based -
 [discord] <zer0condition> even CPUID spoofing could have been done without an HV, if they actually reversed the binaries and found a way to locate the callsites
[discord] <zer0condition> even CPUID spoofing could have been done without an HV, if they actually reversed the binaries and found a way to locate the callsites -
 I know Russian, but can't understand where the main threads are
I know Russian, but can't understand where the main threads are -
 Click to forum in main page
Click to forum in main page -
 [discord] <zer0condition> but then again, the warez scene has not been very impressive lately
[discord] <zer0condition> but then again, the warez scene has not been very impressive lately -
 I see now, the menu isn't working on the mobile version of the site
I see now, the menu isn't working on the mobile version of the site -
 [discord] <zer0condition> https://blog.sunmkt.uk/post/denuvo-analysis/Denuvo 分析 - Sunset 的重构博客
[discord] <zer0condition> https://blog.sunmkt.uk/post/denuvo-analysis/Denuvo 分析 - Sunset 的重构博客来源,CC BY-SA 4.0 协议,gemini-3-pro-preview翻译。\n前言 本文仅供教育目的。Denuvo 可以说是这世上最成功的数字版权管理(DRM)解决方案,因此许多人都对它感兴趣。这篇博客包含了我大量的个人笔记以及与其他逆向工程师(见 致谢)的通信内容,其中包含了关于 Denuvo 近期迭代的信息,很多内容我此前未见公开分享过。\n
-
 I think that the main difficulty is shit like vmprotect etc
I think that the main difficulty is shit like vmprotect etc -
 [discord] <zer0condition> here is the origin where this "crack" came to be
[discord] <zer0condition> here is the origin where this "crack" came to be -
 [discord] <zer0condition> [reply]: VMP is not the most impressive, neither is Themida, if we are comparing it to other commercial protectors in this current day context, the back.engineering people have an idea on good stuff and also anti-cheats like EAC. Riot Vanguard and Faceit use something very similar, you could say the same
[discord] <zer0condition> [reply]: VMP is not the most impressive, neither is Themida, if we are comparing it to other commercial protectors in this current day context, the back.engineering people have an idea on good stuff and also anti-cheats like EAC. Riot Vanguard and Faceit use something very similar, you could say the same -
 [discord] <zer0condition> https://www.youtube.com/watch?v=3LtwqJM3QjgRE//verse 2026: Deobfuscation of a Real World Binary Obfuscator by James McGowan and Bas Zweers
[discord] <zer0condition> https://www.youtube.com/watch?v=3LtwqJM3QjgRE//verse 2026: Deobfuscation of a Real World Binary Obfuscator by James McGowan and Bas ZweersFrom RE//verse 2026, watch James McGowan and Bas Zweers' talk: Deobfuscation of a Real World Binary Obfuscator Talk Slides: https://github.com/AnalogCyberNuke/RE-Verse-2026-Slides/blob/main/Reverse26.pdf We analyze and deobfuscate a real-world commercial binary obfuscator used to protect several pieces of important software including Windows KernelMode game anti-cheat systems. We explain our analysis and deobfuscation processes, including the custom tooling we built along the way which can be generalized to work on other obfuscators. Finally, we present a complete taxonomy of its structure, some deobfuscated binaries, and a sneak peek behind the scenes of some clever anti-cheat systems. For more RE//verse updates, subscribe to our newsletter: https://mailchi.mp/re-verse/reverse-mailing-list-signup
-
 If vmp is well configured, it's not easy to analyze executable for me
If vmp is well configured, it's not easy to analyze executable for me -
 [discord] <zer0condition> this is a really nice talk addressing it by the back.engineering people
[discord] <zer0condition> this is a really nice talk addressing it by the back.engineering people -
 Anti debug is the main issue for me
Anti debug is the main issue for me -
most people have proper tooling for lifting, deobfuscating, rebuilding blah blah, it’s not hard for people who know how advanced obfuscation works
-
 I tried to use Titan in my research, but the result is shit
I tried to use Titan in my research, but the result is shit -
EAC has put out a new obfuscation, similar to the “hungarian tech” by vgk and faceit, have you checked it?
-
look into remill and llvm stuff
-
 [discord] <zer0condition> [reply]: not personally yet, been busy with school, but have heard its similar to it yeah but better
[discord] <zer0condition> [reply]: not personally yet, been busy with school, but have heard its similar to it yeah but better -
gotcha, also please accept the friend request on discord
-
 you can do
you can do
rdtsc a
rdtsc b
cpuid
rdtsc c
rdtsc d
and d-c should not be apparently larger than b-a, I think -
 reasonable xD
reasonable xD -
 that's great
that's great -
 I always thought ACE had the most aggressive hypervisor detection. Surprised EAC is stricter
I always thought ACE had the most aggressive hypervisor detection. Surprised EAC is stricter -
 [discord] <zer0condition> [reply]: nope sadly, their credibility falls alot because they copy-pasted a detection library straight from GitHub onto their code, https://github.com/jonomango/nohvGitHub - jonomango/nohv: Kernel driver for detecting Intel VT-x hypervisors.
[discord] <zer0condition> [reply]: nope sadly, their credibility falls alot because they copy-pasted a detection library straight from GitHub onto their code, https://github.com/jonomango/nohvGitHub - jonomango/nohv: Kernel driver for detecting Intel VT-x hypervisors.Kernel driver for detecting Intel VT-x hypervisors. - jonomango/nohv
-
 [discord] <zer0condition> more like, most of their detection mechanisms are straight from GitHub, it has been confirmed via many credible sources (reverse engineers) by comparing their exection sequence for such checks.
[discord] <zer0condition> more like, most of their detection mechanisms are straight from GitHub, it has been confirmed via many credible sources (reverse engineers) by comparing their exection sequence for such checks. -
 Why can't I catch all rdtsc?
Why can't I catch all rdtsc? -
did u not read
-
he sent it up there long ago
-
^^^^
-
haha jonomangoo
-
 Why can't we reduce the cpu freq that the system sees?
Why can't we reduce the cpu freq that the system sees? -
 really? didn't expected that😆I've never dived into ACE kernel as ACE-lite's kernel driver only added an ob callback to protect the process
really? didn't expected that😆I've never dived into ACE kernel as ACE-lite's kernel driver only added an ob callback to protect the process -
 [discord] <zer0condition> [reply]: yeah, i havent taken a look too in a long time, their protection is also very VMP inspired i should say
[discord] <zer0condition> [reply]: yeah, i havent taken a look too in a long time, their protection is also very VMP inspired i should say -
 .tvm0 lol, they also use it in its usermode code and many other tencent products
.tvm0 lol, they also use it in its usermode code and many other tencent products -
 [discord] <zer0condition> [reply]: (reply to rev1sor1337) TSC doesnt measure frequency, it counts cycles at a fixed rate (invariant TSC on modern CPUs), reducing what the system "sees" would mean applying a constant offset or scaling factor to every TSC read: but that breaks monotonicity guarantees the OS depends on. spinlocks, scheduler quantum, QueryPerformanceCounter all assume TSC moves forward consistently, mess with that and you get watchdog timeouts, TDR, or subtle timing corruption.
[discord] <zer0condition> [reply]: (reply to rev1sor1337) TSC doesnt measure frequency, it counts cycles at a fixed rate (invariant TSC on modern CPUs), reducing what the system "sees" would mean applying a constant offset or scaling factor to every TSC read: but that breaks monotonicity guarantees the OS depends on. spinlocks, scheduler quantum, QueryPerformanceCounter all assume TSC moves forward consistently, mess with that and you get watchdog timeouts, TDR, or subtle timing corruption. -
 [discord] <zer0condition> [reply]: I've already made detailed descriptions on it, please read the blog first.
[discord] <zer0condition> [reply]: I've already made detailed descriptions on it, please read the blog first. -
 [discord] <zer0condition> [reply]: yep
[discord] <zer0condition> [reply]: yep -
 I do see some hypervisor impls intercepts all rdtsc calls and reduce them based on the time vmexit uses
I do see some hypervisor impls intercepts all rdtsc calls and reduce them based on the time vmexit uses -
 and it lags a lot
and it lags a lot -
 [discord] <zer0condition> [reply]: yeah that approach exists too but it has alot of issues.
[discord] <zer0condition> [reply]: yeah that approach exists too but it has alot of issues. -
 [discord] <zer0condition> cummulative drift, monotonicity and also performance yes all applies
[discord] <zer0condition> cummulative drift, monotonicity and also performance yes all applies -
 or to say most public hvs with bypass use such method
or to say most public hvs with bypass use such method -
 [discord] <zer0condition> long sessions that hammer the TSC and you can imagine how the that turns out
[discord] <zer0condition> long sessions that hammer the TSC and you can imagine how the that turns out -
zer0condition
-
I'm working on our project and also finished the EPT hook by the way
-
 [discord] <zer0condition> i am confused, who are you?
[discord] <zer0condition> i am confused, who are you? -
 Reminder that DMAs bypass EPTs unless you do mmio virtualization
Reminder that DMAs bypass EPTs unless you do mmio virtualization -
 Vanguard uses intel's nic driver to perform DMAs
Vanguard uses intel's nic driver to perform DMAs -
 Hi, no I’m running on a 12th Gen Intel Core i5-12600KF. The issue seems different I can’t fully disable it, and the error message doesn’t provide any useful information
Hi, no I’m running on a 12th Gen Intel Core i5-12600KF. The issue seems different I can’t fully disable it, and the error message doesn’t provide any useful information - 21 March 2026 (15 messages)
-
 msinfo32. Verify that its disabled from there. If it isnt, open cmd as admin and type bcdedit /set hypervisorlaunchtype off then restart
msinfo32. Verify that its disabled from there. If it isnt, open cmd as admin and type bcdedit /set hypervisorlaunchtype off then restart -
 I also did this, but it wasn't enough last time that checked it on a core ultra 2XX.
I also did this, but it wasn't enough last time that checked it on a core ultra 2XX. -
 Could you check these registry items:
Could you check these registry items:
https://woshub.com/disable-credential-guard-windows/How to Disable (Enable) Credential Guard in Windows 11 | Windows OS HubThe Credential Guard security feature in the latest versions of Windows protects accounts against theft and unauthorized use, including Pass-the-Hash and Pass-the-Ticket attacks. Credential Guard uses virtualization-based security (VBS) to…
-
 Did you disable every device security option in windows security?
Did you disable every device security option in windows security? -
 That's also required
That's also required -
 After adding those registry entries it worked, but since I also disabled a lot of other things, I'm not sure if it was only because of those regsitry items.
After adding those registry entries it worked, but since I also disabled a lot of other things, I'm not sure if it was only because of those regsitry items. -
 I think so
I think so -
 It always worked for me so far
It always worked for me so far -
 Disabling options in defender and bcdedit
Disabling options in defender and bcdedit -
 In a new machine? Recently?
In a new machine? Recently? -
 They are making it harder though as far as I heard
They are making it harder though as far as I heard -
 Yeah
Yeah -
 25h2
25h2 -
 👍
👍 -
 [discord] <unrustled.jimmies> VBS can be uefi locked and stored as a secure boot efi var and this will force it on no matter the value of any other setting. You can use secconfig.efi, a special tool signed by microsoft to disable it without turning off secure boot or just disable secure boot. See https://learn.microsoft.com/en-us/windows/security/identity-protection/credential-guard/configure?tabs=intune#disable-credential-guard-with-uefi-lock
[discord] <unrustled.jimmies> VBS can be uefi locked and stored as a secure boot efi var and this will force it on no matter the value of any other setting. You can use secconfig.efi, a special tool signed by microsoft to disable it without turning off secure boot or just disable secure boot. See https://learn.microsoft.com/en-us/windows/security/identity-protection/credential-guard/configure?tabs=intune#disable-credential-guard-with-uefi-lock
> bcdedit /set hypervisorlaunchtype off
iirc correctly, hyperdbg can work under hyperv, it just can't work under VBS.Configure Credential GuardLearn how to configure Credential Guard using MDM, Group Policy, or the registry.
- 22 March 2026 (4 messages)
-
 Alr, thanks
Alr, thanks -
 Interesting. Thanks for sharing.
Interesting. Thanks for sharing. -
Joined.
-
Joined.
- 23 March 2026 (2 messages)
-
 [discord] <fexsped> Is this project intel only? What happened to reddbg?
[discord] <fexsped> Is this project intel only? What happened to reddbg? -
 HyperDbg is Intel only for now. RedDbg is archived, not in a working state.
HyperDbg is Intel only for now. RedDbg is archived, not in a working state. - 24 March 2026 (10 messages)
-
How does AMD solve the EPT hook issue if it's called frequently
-
 Joined.
Joined. -
 AMD processors have their own implantation of SLAT, it's called NPT.
AMD processors have their own implantation of SLAT, it's called NPT. -
 I think you could check SimpleSVM project for implemtation of EPT (NPT) hooks there.
I think you could check SimpleSVM project for implemtation of EPT (NPT) hooks there. -
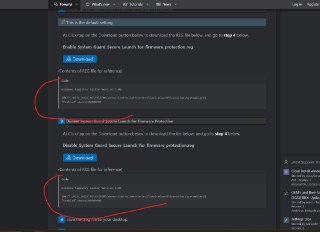
 @ghvv188 take a look at this one too:
@ghvv188 take a look at this one too:
https://www.elevenforum.com/t/enable-or-disable-system-guard-secure-launch-for-firmware-protection-in-windows-11.29233/Enable or Disable System Guard Secure Launch for Firmware...This tutorial will show you how to enable or disable Microsoft Defender System Guard Secure Launch for firmware protection in Windows 10 and Windows 11 Secured-core PCs. Microsoft has worked with...
-
 There are two registry files here that I think last time that we tried to run HyperDbg, running these reg files helped us disabling VBS (Hyper-V).
There are two registry files here that I think last time that we tried to run HyperDbg, running these reg files helped us disabling VBS (Hyper-V). -
-
Try turning off VBS using the method in that link. There's a tool called Toe.bat, and another one for disabling the virtual machine.
-
There was also a script provided by Microsoft that can disable VBS. But every time I restart my computer the first time, it turns off successfully. When I restart again, VBS turns back on automatically. So there might be something wrong with Microsoft's script.
-
 Thank you
Thank you - 26 March 2026 (6 messages)
-
 [discord] <livanec_smaslem> Can I ask why do we allocate 3* 4096 of memory ? 3 times more than the maximum size of VMXON region ? I get that allocating 2* would guarantee we can manually align it, but whats the 3* for ?
[discord] <livanec_smaslem> Can I ask why do we allocate 3* 4096 of memory ? 3 times more than the maximum size of VMXON region ? I get that allocating 2* would guarantee we can manually align it, but whats the 3* for ?
https://cdn.discordapp.com/attachments/962350355839066130/1486575252850086049/image.png?ex=69c60097&is=69c4af17&hm=1f296c83c79b928522e06e6761b334c27981c769ebb80b9c1d46ab03d42237f7& -
 I guess its "just in case", but ExAllocatePool2 already guarantees page-aligned allocations on page-aligned size requests
I guess its "just in case", but ExAllocatePool2 already guarantees page-aligned allocations on page-aligned size requests -
 [discord] <livanec_smaslem> oh yeah you're right.. so this would just be enough ? and hyperdbg is allocating just because
[discord] <livanec_smaslem> oh yeah you're right.. so this would just be enough ? and hyperdbg is allocating just because
ExAllocatePool2(POOL_FLAG_NON_PAGED, 4096, 'vmxo'); -
 It's allocating to make sure it doesnt overwrite pages before and after it when it aligns the allocation afaik
It's allocating to make sure it doesnt overwrite pages before and after it when it aligns the allocation afaik -
 That was how its in hypervisor from scratch tutorials
That was how its in hypervisor from scratch tutorials -
 But yeah. This is a fact
But yeah. This is a fact - 27 March 2026 (52 messages)
-
 3 pages to align a page from an allocator that already returns page aligned memory.. whoever the fuck taught you this is brain damaged and needs to be retroactively aborted
3 pages to align a page from an allocator that already returns page aligned memory.. whoever the fuck taught you this is brain damaged and needs to be retroactively aborted -
 Then what it is for
Then what it is for -
 #define ALIGNMENT_PAGE_SIZE 4096
#define ALIGNMENT_PAGE_SIZE 4096
Yeah. There was no such allocation -
 No we do in part 3's source. It wasn't 3 though.
No we do in part 3's source. It wasn't 3 though.
int VMXONSize = 2 * VMXON_SIZE; -
 [discord] <livanec_smaslem> [reply]: in hyperdbg source it is 3. they also add ALIGNMENT_PAGE_SIZE which is another 4096. i dont understand the reasoning
[discord] <livanec_smaslem> [reply]: in hyperdbg source it is 3. they also add ALIGNMENT_PAGE_SIZE which is another 4096. i dont understand the reasoning
https://cdn.discordapp.com/attachments/962350355839066130/1486976028139192431/image.png?ex=69c775d7&is=69c62457&hm=7ab6484185598200a6d4c252193726dc3be56ceca49a17b30f388cccfe690a2b& -
I’ve already installed the HyperDbg VMM driver on my physical machine. Do I still need to install the VMM driver on the Windows 10 virtual machine in VMware?
-
 If you are using HyperDbg in the debugger mode, you don't need to install the driver or anything on your physical machine. You just need to install drivers in the guest while HyperDbg on the side of the host acts as a (user-mode) serial communication app.
If you are using HyperDbg in the debugger mode, you don't need to install the driver or anything on your physical machine. You just need to install drivers in the guest while HyperDbg on the side of the host acts as a (user-mode) serial communication app. -
thankyou
-
 I was waiting for your justification
I was waiting for your justification -

-
 Ask the author of code (Sina I guess), my guess is that he didn't know it returned a page aligned address
Ask the author of code (Sina I guess), my guess is that he didn't know it returned a page aligned address -
 I think that, by default, if we allocate 4096 bytes, Windows gives us an aligned memory address (at least from what I vaguely remember).
I think that, by default, if we allocate 4096 bytes, Windows gives us an aligned memory address (at least from what I vaguely remember). -
 Yep it does
Yep it does -
 [discord] <fexsped> I was reading [here](https://rayanfam.com/topics/hypervisor-from-scratch-part-2/) about how VMX needs to be enabled through cr4 and then having to switch to vmx operating mode using VMXON. Does this VMXON take effect only on the current core? how do type2 hypervisors work while also allowing the underlying system to function without beint in VMX operating mode?Hypervisor From Scratch – Part 2: Entering VMX Operation
[discord] <fexsped> I was reading [here](https://rayanfam.com/topics/hypervisor-from-scratch-part-2/) about how VMX needs to be enabled through cr4 and then having to switch to vmx operating mode using VMXON. Does this VMXON take effect only on the current core? how do type2 hypervisors work while also allowing the underlying system to function without beint in VMX operating mode?Hypervisor From Scratch – Part 2: Entering VMX OperationWe write about Windows Internals, Hypervisors, Linux, and Networks.
-
 Yes, vmxon affects only the current CPU thread. It's totally possible to enable VMX only for a subset of the cores. What problems do you see in that scenario?
Yes, vmxon affects only the current CPU thread. It's totally possible to enable VMX only for a subset of the cores. What problems do you see in that scenario? -
 Vmx mode has to be enabled for any vt-x instruction to be recognized
Vmx mode has to be enabled for any vt-x instruction to be recognized -
 So if a core is hypervised, the vmx mode must be on. You might be confusing vmx root and non root operating modes
So if a core is hypervised, the vmx mode must be on. You might be confusing vmx root and non root operating modes -
 [discord] <fexsped> so in a type2 hypervisor a certain number of cores are in VMXON mode at any given time and the others are reserved for the OS? is that what giving a VM a certain number of cores do?
[discord] <fexsped> so in a type2 hypervisor a certain number of cores are in VMXON mode at any given time and the others are reserved for the OS? is that what giving a VM a certain number of cores do? -
 All of the cores are usually "vmxon"-ed via IPI
All of the cores are usually "vmxon"-ed via IPI -
 [discord] <fexsped> if all cores are in vmx mode doesnt that mean they should be running a vmm and not an os?
[discord] <fexsped> if all cores are in vmx mode doesnt that mean they should be running a vmm and not an os? -
 It only means that it may use vmx instructions.
It only means that it may use vmx instructions. -
 Vmx mode means cpu is capable of vt-x
Vmx mode means cpu is capable of vt-x -
 Vmx root mode is hypervisor
Vmx root mode is hypervisor -
 Vmx non root mode is the guest
Vmx non root mode is the guest -
 [discord] <fexsped> so thats all vmxon does?
[discord] <fexsped> so thats all vmxon does? -
 Yup
Yup -
 [discord] <fexsped> whats up with that cr4 bit you have to set?
[discord] <fexsped> whats up with that cr4 bit you have to set? -
 It's to enable vt-x for the cpu
It's to enable vt-x for the cpu -
 [discord] <fexsped> so you need to enable vt-x twice
[discord] <fexsped> so you need to enable vt-x twice -
 It doesn't have to do anything with guest/host separation
It doesn't have to do anything with guest/host separation -
 No. Only one time
No. Only one time -
 CR4 is usually set up by the bios and locked, so you can't modify it in runtime
CR4 is usually set up by the bios and locked, so you can't modify it in runtime -
 VMX bit enables vt-x extension. Vmxon loads the vmxon region required by each logical core
VMX bit enables vt-x extension. Vmxon loads the vmxon region required by each logical core -
 [discord] <fexsped> oh that makes sense with the BIOS setting to enable virtualization
[discord] <fexsped> oh that makes sense with the BIOS setting to enable virtualization -
 Vmxon is required for other instructions like vmresume, vmlaunch
Vmxon is required for other instructions like vmresume, vmlaunch -
 Yes, thats what it does
Yes, thats what it does -
 [discord] <fexsped> [reply]: the vmcs?
[discord] <fexsped> [reply]: the vmcs? -
 Vmcs and vmxon region are different
Vmcs and vmxon region are different -
 [discord] <fexsped> what does this vmxon region contain? All I find is this in the intel manual:
[discord] <fexsped> what does this vmxon region contain? All I find is this in the intel manual:
> Before executing VMXON, software should write the VMCS revision identifier (see Section 26.2) to the VMXON
> region. (Specifically, it should write the 31-bit VMCS revision identifier to bits 30:0 of the first 4 bytes of the
> VMXON region; bit 31 should be cleared to 0.) -
 Treat that region as opaque
Treat that region as opaque -
 [discord] <fexsped> so just give a page to vmxon and its gods plan?
[discord] <fexsped> so just give a page to vmxon and its gods plan? -
 Yes, exactly
Yes, exactly -
 [discord] <fexsped> alr lol
[discord] <fexsped> alr lol -
 Implementation specific
Implementation specific -
 Except the revision identifier
Except the revision identifier -
 [discord] <fexsped> also I was wondering why this guide is on windows
[discord] <fexsped> also I was wondering why this guide is on windows -
 [discord] <fexsped> wouldnt it be easier on linux?
[discord] <fexsped> wouldnt it be easier on linux? -
 It's same for everything
It's same for everything -
 We hyperjack Windows so we need Windows specific apis to allocate memory and run on all other cores
We hyperjack Windows so we need Windows specific apis to allocate memory and run on all other cores -
 Otherwise, the process is same for say, hyperjacking linux. Or writing a separation kernel
Otherwise, the process is same for say, hyperjacking linux. Or writing a separation kernel -
 [discord] <fexsped> how far along is porting hyperdbg to linux?
[discord] <fexsped> how far along is porting hyperdbg to linux? -
 [discord] <fexsped> I see why this was done for windows first as there is a lot more reversing potential to gain out of it
[discord] <fexsped> I see why this was done for windows first as there is a lot more reversing potential to gain out of it - 30 March 2026 (1 messages)
-
Joined.
- 31 March 2026 (3 messages)
-
/report
-
 Reported ⚜️LEBAP⚜️ [7001057901] to admins.
Reported ⚜️LEBAP⚜️ [7001057901] to admins. -

- 02 Mar 2026 (1)
- 03 Mar 2026 (1)
- 05 Mar 2026 (8)
- 06 Mar 2026 (3)
- 07 Mar 2026 (1)
- 08 Mar 2026 (2)
- 09 Mar 2026 (1)
- 13 Mar 2026 (1)
- 14 Mar 2026 (2)
- 15 Mar 2026 (2)
- 18 Mar 2026 (2)
- 19 Mar 2026 (21)
- 20 Mar 2026 (105)
- 21 Mar 2026 (15)
- 22 Mar 2026 (4)
- 23 Mar 2026 (2)
- 24 Mar 2026 (10)
- 26 Mar 2026 (6)
- 27 Mar 2026 (52)
- 30 Mar 2026 (1)
- 31 Mar 2026 (3)