- 01 September 2024 (55 messages)
-
is it possible to use a hypervisor to track exception handling in windows?
For example:
try{
exception page fault
}
catch (err) {
not debugger
}.
There is a tricky defense mechanism that causes a page error and is handled in the driver itself (Windbg does not see an exception) -
 Yes. You can use the !exception command combined with the event short circuiting mechanism.
Yes. You can use the !exception command combined with the event short circuiting mechanism.
By default, if an exception/fault/interrupt happens in the system, HyperDbg re-injects it to the guest.
You can decide whether you want it to be injected to the guest and be handled by Windows or drop it and ignore it by short circuiting it.
Please check:
https://docs.hyperdbg.org/tips-and-tricks/misc/event-short-circuitingEvent short-circuiting | HyperDbg DocumentationThe event short-circuiting and ignoring mechanism in HyperDbg
-
we don't need to ignore the exception, but we need to track where the handler of this exception is located (the code in catch).
-
 So, you need to find the handler using a simple script using the same !exception command.
So, you need to find the handler using a simple script using the same !exception command. -
Yes, that's right.... what should the script look like for !exception
-
 I'm not sure how SEH works these days. A few years ago, it was like putting the address of SEH Handler in the stack but I'm not sure if it still works the same way.
I'm not sure how SEH works these days. A few years ago, it was like putting the address of SEH Handler in the stack but I'm not sure if it still works the same way. -
 You need to check how Microsoft implemented the SEH in newer Windows versions.
You need to check how Microsoft implemented the SEH in newer Windows versions. -
I tried to put a breakpoint in windbg on the handler function in the idt table, but the system was hanging
-
-
 This is also a unique aspect of HyperDbg. You cannot trace instructions in ISRs (IDT functions) in WinDbg but you can do it in HyperDbg. 🙂
This is also a unique aspect of HyperDbg. You cannot trace instructions in ISRs (IDT functions) in WinDbg but you can do it in HyperDbg. 🙂
Make sure to use the instrumentation step-in instead of regular step-in.
https://docs.hyperdbg.org/commands/debugging-commands/ii (instrumentation step-in) | HyperDbg DocumentationDescription of the 'i' command in HyperDbg.
-
 Nope. It's possible in HyperDbg. But it's not possible in WinDbg.
Nope. It's possible in HyperDbg. But it's not possible in WinDbg. -
 But, there should be articles online that they already analyzed SEH. I think this way of analyzing SEH from IDT entries is so fundamental and time consuming. There should be better and easier ways for analyzing SEH. 🤔
But, there should be articles online that they already analyzed SEH. I think this way of analyzing SEH from IDT entries is so fundamental and time consuming. There should be better and easier ways for analyzing SEH. 🤔 -
if we are talking about the driver, is there a VEH?
-
 VEH?
VEH? -
vector exception handling in 64 windows
-
 Unfortunately, I'm not familiar with it.
Unfortunately, I'm not familiar with it. -
so you can use hyperdbg to analyze the entire chain?
-
 Yes. But you need to use the 'i' command instead of 't'.
Yes. But you need to use the 'i' command instead of 't'. -
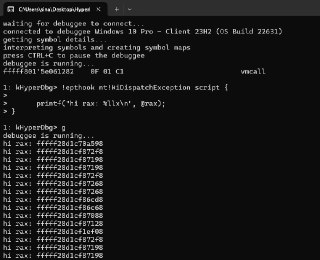
tell me please how to correctly create a script for !exception to stop at KiDispatchException
-
-
 Can you send your script here? What's the reason for BSOD?
Can you send your script here? What's the reason for BSOD? -
I haven't used the script yet. I just put it on !epthook on KiDispatchException
-
 Use a simple script like a simple logging printf and if it crashes the system, send us the WinDbg's analyze -v results.
Use a simple script like a simple logging printf and if it crashes the system, send us the WinDbg's analyze -v results. -
something like this !epthook script {printf (@rip)}?
-
 Yes.
Yes. -
 @HughEverett can i access code safe buffer from script somehow?
@HughEverett can i access code safe buffer from script somehow?
im trying
!monitor x 00d6d049 l 2 buffer 10 asm code {mov byte ptr ds:[rcx], 20} script {
printf("%x \n",dq(rcx));
}
but getting
(20:50:24.230 - core : 1 - vmx-root? yes) [+] Information (DebuggerPerformRunScript:1730) | err, ScriptEngineExecute, function = FUNC_DQ -
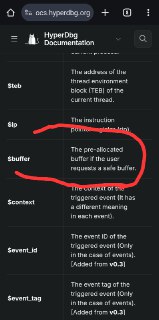
 Safe buffer pointer is available at the '$buffer' pseudo-register.
Safe buffer pointer is available at the '$buffer' pseudo-register. -

-
 You're trying to dereference an invalid address (in this case @rcx). That's why you see that error.
You're trying to dereference an invalid address (in this case @rcx). That's why you see that error. -
 damn... again i didnt RTFM :D
damn... again i didnt RTFM :D -
 thanks
thanks -
-
-
-
 @HughEverett
@HughEverett
hmm
!monitor x 00d6d049 l 2 buffer 10 asm code {mov byte ptr ds:[rcx], 20} script {
printf("TRIGGER %x\n",db($buffer));
}
it prints 0 for some reason,, -
 You can use the buffer which is available in rcx. <— from docs
You can use the buffer which is available in rcx. <— from docs -
 That's weird. Will it happen if you don't use (test trap off)? I mean just using the !epthook will crash it?
That's weird. Will it happen if you don't use (test trap off)? I mean just using the !epthook will crash it? -
 That's an error for sure. Could you please open an issue for it on GitHub?
That's an error for sure. Could you please open an issue for it on GitHub? -
test trap off or enabled.... BSOD
-
 Right now, I'm on a trip. I'll fix them all hopefully next week.
Right now, I'm on a trip. I'll fix them all hopefully next week. -
-
 Is it hooked in a normal system? I mean is there any anti-debugging/cheating software working on the target system?
Is it hooked in a normal system? I mean is there any anti-debugging/cheating software working on the target system? -
 I ask it because it seems that people had the same problem for this function:
I ask it because it seems that people had the same problem for this function:
https://www.unknowncheats.me/forum/anti-cheat-bypass/620722-hooking-kidispatchexception-help.htmlHooking KiDispatchException Need helphi guys ! I hooked the KiDispatchException using ept . I use here to intercept kernel access exceptions. My goal is to make a safe copy function that
-
system work normal mode
-
 Other than that, can you test the same script (don't use @rip. Show @rcx instead) using !epthook2 command?
Other than that, can you test the same script (don't use @rip. Show @rcx instead) using !epthook2 command? -
one minute
-
i use hyperdbg with trap flag in cpuid
-
-
-
 sure
sure -
 That's weird. Something irregular is happening to this function. Maybe it's an immediate patchguard check. I have to inspect it. Please create a GitHub issue for it, so we can investigate and fix it.
That's weird. Something irregular is happening to this function. Maybe it's an immediate patchguard check. I have to inspect it. Please create a GitHub issue for it, so we can investigate and fix it. -
os windows 10 - vmware 17
-
 Joined.
Joined. -
 @HughEverett https://github.com/HyperDbg/HyperDbg/issues/471Buffer not accessible in script · Issue #471 · HyperDbg/HyperDbg
@HughEverett https://github.com/HyperDbg/HyperDbg/issues/471Buffer not accessible in script · Issue #471 · HyperDbg/HyperDbg.start path C:\dbg\getch.exe g !monitor x 00007ff730371016 l 8 buffer 10 asm code {mov byte ptr ds:[rcx], 20; ret;} script { printf("TRIGGER %x\n",db($buffer)); } type any letter and pres...
-
 Thanks
Thanks - 03 September 2024 (11 messages)
-
 [discord] <oi_its_me> I'm getting build errors even after installing the latest WDK, SDK, and VS2022
[discord] <oi_its_me> I'm getting build errors even after installing the latest WDK, SDK, and VS2022
```
Severity Code Description Project File Line Suppression State Details
Error MSB8020 The build tools for WindowsKernelModeDriver10.0 (Platform Toolset = 'WindowsKernelModeDriver10.0') cannot be found. To build using the WindowsKernelModeDriver10.0 build tools, please install WindowsKernelModeDriver10.0 build tools. Alternatively, you may upgrade to the current Visual Studio tools by selecting the Project menu or right-click the solution, and then selecting "Retarget solution". hyperlog C:\Program Files\Microsoft Visual Studio\2022\Community\MSBuild\Microsoft\VC\v170\Microsoft.CppBuild.targets 456
```
Any thoughts? I understand that it''s saying that I need WDK 10.0, but I have it installed. -
 [discord] <oi_its_me> Installed everything from here: https://learn.microsoft.com/en-us/windows-hardware/drivers/download-the-wdkDownload the Windows Driver Kit (WDK) - Windows drivers
[discord] <oi_its_me> Installed everything from here: https://learn.microsoft.com/en-us/windows-hardware/drivers/download-the-wdkDownload the Windows Driver Kit (WDK) - Windows driversDownload instructions for the latest released version of the Windows Driver Kit (WDK)
-
 [discord] <oi_its_me> I'm getting ```Severity Code Description Project File Line Suppression State Details
[discord] <oi_its_me> I'm getting ```Severity Code Description Project File Line Suppression State Details
Error C1083 Cannot open include file: 'SDK/Imports/HyperDbgHyperLogImports.h': No such file or directory hyperdbg_driver C:\Users\me\Desktop\HyperDbg\hyperdbg\include\SDK\Examples\hyperdbg_driver\header\pch.h 58 ``` and similar errors. -
 [discord] <oi_its_me> I have the compiled executable, I was wondering if I should worry about the rror?
[discord] <oi_its_me> I have the compiled executable, I was wondering if I should worry about the rror? -
 [discord] <oi_its_me> I'm pretty sure I'm okay.
[discord] <oi_its_me> I'm pretty sure I'm okay. -
 [discord] <oi_its_me> Last question: when following “Disable DSE by Attaching WinDbg”, it states
[discord] <oi_its_me> Last question: when following “Disable DSE by Attaching WinDbg”, it states
> and no need for WinDbg anymore.
Is this persistent across restarts? If I shut down my host VM and target VM, I still don’t have to repeat the WinDbg step? I could restart my VM or HyperDbg without doing this step? -
-
 Hey!
Hey!
Is it only for HyperDbg? Could you compile other random drivers? Are you sure you clone HyperDbg with --recursive flag? -
 Each time you need to open WinDbg if you restart. If you need a persistent method, you need to use EfiGuard:
Each time you need to open WinDbg if you restart. If you need a persistent method, you need to use EfiGuard:
https://github.com/Mattiwatti/EfiGuardGitHub - Mattiwatti/EfiGuard: Disable PatchGuard and Driver Signature Enforcement at boot timeDisable PatchGuard and Driver Signature Enforcement at boot time - Mattiwatti/EfiGuard
-
 If a page-fault relates to the inner working of the operating system (e.g., for bringing a page into the memory), then WinDbg won't intercept it. You can still use HyperDbg's !exception command, it intercepts all exceptions/faults/interrupts.
If a page-fault relates to the inner working of the operating system (e.g., for bringing a page into the memory), then WinDbg won't intercept it. You can still use HyperDbg's !exception command, it intercepts all exceptions/faults/interrupts. -
 If a driver handled the exception in a SEH try...catch, still WinDbg won't intercept it, but again HyperDbg intercepts it as it gets the events from the hypervisor before the operating system.
If a driver handled the exception in a SEH try...catch, still WinDbg won't intercept it, but again HyperDbg intercepts it as it gets the events from the hypervisor before the operating system. - 04 September 2024 (8 messages)
-
there is a kernel driver with a protection mechanism. It calls 20-30 consecutive exceptions(page fault) through the for loop. the latest version of hyperdbg(v1.0) does not catch them (apparently does not have time), and the driver itself writes "failed to connect the device"
-

-
 Yes. There is a strcmp and strncmp function in the script engine, please check:
Yes. There is a strcmp and strncmp function in the script engine, please check:
https://docs.hyperdbg.org/commands/scripting-language/functions/strings/strcmpstrcmp | HyperDbg DocumentationDescription of the 'strcmp' function in HyperDbg Scripts
-
 Other than that, don't forget that $pname is 16 byte long container. So, some parts of the process name might not be included.
Other than that, don't forget that $pname is 16 byte long container. So, some parts of the process name might not be included. -
 No, that's not possible. HyperDbg gets the #PFs directly from CPU. If !exception didn't show any results, then no page-fault happens. Can you show what script you used for detecting page-faults?
No, that's not possible. HyperDbg gets the #PFs directly from CPU. If !exception didn't show any results, then no page-fault happens. Can you show what script you used for detecting page-faults? -
 [discord] <oi_its_me> I’m sure! Sorry for the late response. Ive definitely built recursively. I’ll try again when I get home.
[discord] <oi_its_me> I’m sure! Sorry for the late response. Ive definitely built recursively. I’ll try again when I get home. -
!exception script {if (@rip > .my_variable-B17F0 && @rip < .my_variable+8AA810 ) {printf("EXCEPTION :\n RAX:%p\n RBX:%p\n RCX:%p\n RDX:%p\n RIP:%p\n CONTEXT:%p\n", @rax, @rbx, @rcx, @rdx, @rip, $context);} }
-
 It's kinda not reasonable to intercept all exceptions even though it's possible. (it's also mentioned in the documentation). Have you tried to intercept only page-faults?
It's kinda not reasonable to intercept all exceptions even though it's possible. (it's also mentioned in the documentation). Have you tried to intercept only page-faults?
Sth like (0xe which is for page-fault is added):
!exception 0xe script {if (@rip > .my_variable-B17F0 && @rip < .my_variable+8AA810 ) {printf("EXCEPTION :\n RAX:%p\n RBX:%p\n RCX:%p\n RDX:%p\n RIP:%p\n CONTEXT:%p\n", @rax, @rbx, @rcx, @rdx, @rip, $context);} } - 05 September 2024 (32 messages)
-
in the analysis, I would like to know which exceptions are used in general...🙄
-
 That's probably not a good idea.
That's probably not a good idea. -
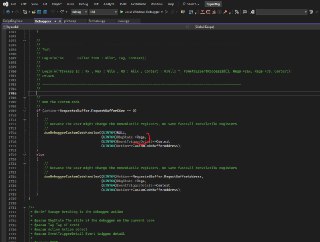
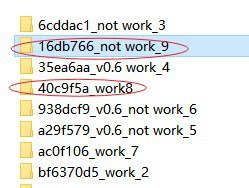
 Eduard I went through the code and it seems that we create a custom buffer for each ACTION, not each EVENT.
Eduard I went through the code and it seems that we create a custom buffer for each ACTION, not each EVENT. -
 Which basically means both the assembly code and the script has their own independent free buffer.
Which basically means both the assembly code and the script has their own independent free buffer. -
 So it's not possible to access each other's buffer, right?
So it's not possible to access each other's buffer, right? -
 Not sure if it's a good idea to make it event specific instead of action specific.
Not sure if it's a good idea to make it event specific instead of action specific. -
 Yes, the buffers are at different addresses.
Yes, the buffers are at different addresses. -
 And there's no way to pass action buffer address to script via register?
And there's no way to pass action buffer address to script via register? -
 I saw that structure with guest registers, but not completely sure how they work
I saw that structure with guest registers, but not completely sure how they work -
 I think it's better to wait for the assembly code to be ready in the script engine instead of changing the design. Because having an independent buffer seems to be a more reasonable option. 🤔
I think it's better to wait for the assembly code to be ready in the script engine instead of changing the design. Because having an independent buffer seems to be a more reasonable option. 🤔 -
 The registers structure is shared.
The registers structure is shared. -
 I mean this one:
I mean this one: -

-
 So, basically if you change anything here it changes on both the script and the assembly code.
So, basically if you change anything here it changes on both the script and the assembly code. -
 But that seems not to be the best option as we need to somehow modify registers and save them somewhere. 🤔
But that seems not to be the best option as we need to somehow modify registers and save them somewhere. 🤔 -
 Regarding this issue:
Regarding this issue:
https://github.com/HyperDbg/HyperDbg/issues/469
It seems that the routines for validating whether a physical address is correct or not correct is not working properly.
Here is how we check whether a physical address is valid or not valid:
https://github.com/HyperDbg/HyperDbg/blob/ceca0ae762b09ec9a8d55c94fcd62332e3657e04/hyperdbg/hyperhv/code/memory/AddressCheck.c#L120
But it seems to be not correct for the MMIO addresses. @honorary_bot do you have an idea for this. 🤔Invalid Physical Address Error in !monitor · Issue #469 · HyperDbg/HyperDbgDescribe the bug The address 7FFDDF8000 is a valid MMIO address, but when using!monitor, it returns the error: err, invalid physical address (c0000052)`. Screenshots OS: [Win11 23H2 22631.4037] Pro...
-
 I wonder what you mean by valid or not valid physical address? The whole system address space is accessible, limited only y the CPU physical address width.
I wonder what you mean by valid or not valid physical address? The whole system address space is accessible, limited only y the CPU physical address width. -
 I see, you're just checking it's not beyond max addressable phys address
I see, you're just checking it's not beyond max addressable phys address -
 I would ask where 7FFDDF8000 comes from. Since it's just checked against cpuid physaddr bits and fails.
I would ask where 7FFDDF8000 comes from. Since it's just checked against cpuid physaddr bits and fails. -
 Though I just checked my 13th gen, it has 39 phys bits, so 7FFDDF8000 fits
Though I just checked my 13th gen, it has 39 phys bits, so 7FFDDF8000 fits -
 The easiest thing to do is probably log EventDetails->Options.OptionalParam1 and EventDetails->Options.OptionalParam2 params, since it's hard to track the code on github on a phone :)
The easiest thing to do is probably log EventDetails->Options.OptionalParam1 and EventDetails->Options.OptionalParam2 params, since it's hard to track the code on github on a phone :) -
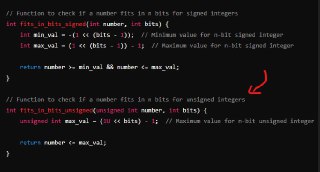
 For me it also has 39 bits. I wrote a program to check it and it seems our checking function fails here.
For me it also has 39 bits. I wrote a program to check it and it seems our checking function fails here. -
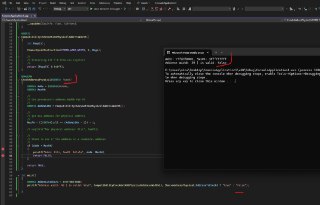
 You're right it fits within 39 bits. It seems that we computed and compared it against a signed value.
You're right it fits within 39 bits. It seems that we computed and compared it against a signed value. -
 And as basically a physical address is considered as an unsigned value. Just we need such a change in our code:
And as basically a physical address is considered as an unsigned value. Just we need such a change in our code: -
 why is it addrwidth - 1 ?
why is it addrwidth - 1 ? -
 Yes, that's the problem. You catch it correctly.
Yes, that's the problem. You catch it correctly. -
 it should be just (1ull << physaddrwidth) - 1
it should be just (1ull << physaddrwidth) - 1 -
 Exactly
Exactly -
 ok, but what about returning value from action ? i think i found out something similar
ok, but what about returning value from action ? i think i found out something similar -
Joined.
-
 I tried to reproduce the error but it works perfectly on my machine. Are you sure you're using the latest version from the 'dev' branch?
I tried to reproduce the error but it works perfectly on my machine. Are you sure you're using the latest version from the 'dev' branch? -
 works fine for me for more than 15 minutes, still without any error!
works fine for me for more than 15 minutes, still without any error! - 06 September 2024 (3 messages)
-
I'm using the master branch🤔. What's the difference?
-
Joined.
-
 The 'dev' branch is always a candidate for the next release and contains all of the updates (fixed issues).
The 'dev' branch is always a candidate for the next release and contains all of the updates (fixed issues). - 08 September 2024 (11 messages)
-
Joined.
-
Joined.
-
 It's been a while since HyperDbg's first release, and we realized our initial assumptions for the command parser won’t fully meet new demands. After redesigning and extensive testing, HyperDbg v0.10.1 now comes with a brand-new parser! 💫😼
It's been a while since HyperDbg's first release, and we realized our initial assumptions for the command parser won’t fully meet new demands. After redesigning and extensive testing, HyperDbg v0.10.1 now comes with a brand-new parser! 💫😼
Check it out:
https://github.com/HyperDbg/HyperDbg/releases/tag/v0.10.1Release v0.10.1 · HyperDbg/HyperDbgHyperDbg v0.10.1 is released! If you’re enjoying HyperDbg, don’t forget to give a star 🌟 on GitHub! Please visit Build & Install to configure the environment for running HyperDbg. Check out the...
-
 Changelog
Changelog
————————————
## [0.10.1.0] - 2024-09-08
New release of the HyperDbg Debugger.
### Added
- Added feature to pause the debuggee immediately upon connection
- The '.debug' command now supports pausing the debuggee at startup
- Export SDK API for assembling instructions
- The 'struct' command now supports a path as output
- Export SDK API closing connection to the remote debuggee
- Automated tests for the main command parser
- Export SDK APIs for stepping and tracing instructions
- Export SDK APIs for tracking execution
### Changed
- HyperDbg command-line comment sign is changed from '#' to C-like comments ('//' and '/**/')
- Integrating a new command parser for the regular HyperDbg commands
- Fix showing a list of active outputs using the 'output' command
- Fix the issue of passing arguments to the '.start' command
- Fix the problem with parsing multiple spaces within the events (#420)
- Fix the problem with escaping '{' in the command parser (#421)
- Fix nested brackets issues in the main command parser
- Fix script engine bugs on order of passing arguments to functions (#453)
- Fix the script test case for factorial computation
- Fix the script test case for computation iterative Fibonacci
- Fix miscomputation of physical address width for physical address validity checks (#469) -
 Many thanks to @Reverser69, @xmaple555, @S4l3H, and Behrooz for their valuable contributions that made this release possible.
Many thanks to @Reverser69, @xmaple555, @S4l3H, and Behrooz for their valuable contributions that made this release possible. -
 [discord] <oi_its_me> Just clarifying, it should be possible to run HyperDbg in a VM and debug a nested VM?
[discord] <oi_its_me> Just clarifying, it should be possible to run HyperDbg in a VM and debug a nested VM? -
 Do you mean running hyperdbg on a VM to debug the kernel of another VM?
Do you mean running hyperdbg on a VM to debug the kernel of another VM? -
 [discord] <oi_its_me> [reply]: Run HyperDbg within a VM and then have VMware within that VM (the nested VM). And then use HyperDbg to debug the nested VM.
[discord] <oi_its_me> [reply]: Run HyperDbg within a VM and then have VMware within that VM (the nested VM). And then use HyperDbg to debug the nested VM. -
 As long as HyperDbg has a serial connection and a virtualization environment (like VMX in a physical machine or a nested VMX), then it could be used. Please refer to:
As long as HyperDbg has a serial connection and a virtualization environment (like VMX in a physical machine or a nested VMX), then it could be used. Please refer to:
https://docs.hyperdbg.org/getting-started/attach-to-hyperdbg/debug#vmware-workstation-two-vmsAttach to a remote machine | HyperDbg DocumentationRemote debugging in VMI Mode and Debugger Mode
-
 Joined.
Joined. -
 [discord] <oi_its_me> Yep, I've tried following that:
[discord] <oi_its_me> Yep, I've tried following that:
```
HyperDbg> .debug remote namedpipe \\.\pipe\HyperDbgPipe
err, occurred while connecting to the server (2)
is the virtual machine running?
```
and I see `windbg` is connect
```
Connected to target 169.254.3.39 on port 50000 on local IP 192.168.1.155.
You can get the target MAC address by running .kdtargetmac command.
Connected to Windows 10 19041 x64 target at (Sun Sep 8 16:21:04.859 2024 (UTC - 7:00)), ptr64 TRUE
Kernel Debugger connection established.
Symbol search path is: srv*
Executable search path is:
Windows 10 Kernel Version 19041 MP (1 procs) Free x64
Edition build lab: 19041.1.amd64fre.vb_release.191206-1406
Kernel base = 0xfffff801`7f402000 PsLoadedModuleList = 0xfffff801`8002c2b0
System Uptime: 0 days 0:00:58.558
```
I have the serial port set
```
\\.\pipe\HyperDbgDebug
```
And still get the error. Thoughts? I'm even able to ping the nested machine. I conect to the nested VM with the `windbg` command:
```
windbg -k net:port=50000,key=3hub72ixqtoq5.xitddgwo0m9c.2ggyaam1f8y1m.yiz0pebmf0ah
``` - 09 September 2024 (1 messages)
-
- 10 September 2024 (47 messages)
-
-
 That's not a big deal. If you could not use kdnet to disable DSE or PatchGuard, you could still use HyperDbg either by configuring EfiGuard, or disabling DSE from the boot menu.
That's not a big deal. If you could not use kdnet to disable DSE or PatchGuard, you could still use HyperDbg either by configuring EfiGuard, or disabling DSE from the boot menu.
Please see this video for more information : https://www.youtube.com/watch?v=MDZ9zYfqo50&ab_channel=OpenSecurityTraining2Dbg3301: HyperDbg 02 04 HyperDbg Lab SetupView the full free MOOC at https://ost2.fyi/Dbg3301. This course is an introductory guide to HyperDbg debugger, guiding you through the initial steps of using HyperDbg, covering essential concepts, principles, debugging functionalities, along with practical examples and numerous reverse engineering methods that are unique to HyperDbg. Whether you have an interest in reverse engineering or seek to elevate your reverse engineering skills with hypervisor-assisted approaches, this course provides a solid foundation for starting your journey.
-
 Disable passing #DBs to the target debuggee?
Disable passing #DBs to the target debuggee? -
 Not sure if I understand what you mean.
Not sure if I understand what you mean. -
yes
-
There is a defense mechanism. He somehow very cunningly detects the interception of exceptions in hyperdbg (!exception). How can this be? the driver is on ring 0, the hypervisor is running on -1
-
 Does local work without windbg on just VBS has to be disabled ? Or do you still need to have Windbg connected via pipe even if your debugging local ?
Does local work without windbg on just VBS has to be disabled ? Or do you still need to have Windbg connected via pipe even if your debugging local ? -

-
 You can decide whether you want to pass or block the #DB using the short-circuiting mechanism (event_sc).
You can decide whether you want to pass or block the #DB using the short-circuiting mechanism (event_sc). -
 For HyperDbg being in kernel mode or user mode is not important, based on the condition that you have (like whether you want to block or not to block e.g., by checking registers), you can either pass or not pass #DBs.
For HyperDbg being in kernel mode or user mode is not important, based on the condition that you have (like whether you want to block or not to block e.g., by checking registers), you can either pass or not pass #DBs. -
 VBS needs to be disabled, but if you can bypass Driver Signature Enforcement, you don't need WinDbg.
VBS needs to be disabled, but if you can bypass Driver Signature Enforcement, you don't need WinDbg. -
 For example, you can disable DSE from the boot menu (windbg is not needed), or even better you can use EfiGuard (again windbg is not needed)
For example, you can disable DSE from the boot menu (windbg is not needed), or even better you can use EfiGuard (again windbg is not needed) -
 I want to able to reverse a crack using hyperdbg because it see's everything i throw at it so far.
I want to able to reverse a crack using hyperdbg because it see's everything i throw at it so far. -
 WinDbg is one of the ways you might want to use to disable DSE. Once HyperDbg is loaded, you could disconnected windbg.
WinDbg is one of the ways you might want to use to disable DSE. Once HyperDbg is loaded, you could disconnected windbg. -
 Didn't understand. 🤔
Didn't understand. 🤔
What does it see? -
 My debugger , procmon, other debugging monitors , api monitor and so on
My debugger , procmon, other debugging monitors , api monitor and so on -
 was hoping to use a VM with hyperdbg and use !measure to hide .. hopefully
was hoping to use a VM with hyperdbg and use !measure to hide .. hopefully -
 The !measure is for anti hypervisor
The !measure is for anti hypervisor -
 It might also not work as expected as we didn't test it for years.
It might also not work as expected as we didn't test it for years. -
 lol noooo .. ok
lol noooo .. ok -
 so is kernel debugging the only way I can reverse this crack on vmware ?
so is kernel debugging the only way I can reverse this crack on vmware ? -
 But generally, using HyperDbg is considered stealthier as HyperDbg doesn't use any debugging api compare to other classic debuggers.
But generally, using HyperDbg is considered stealthier as HyperDbg doesn't use any debugging api compare to other classic debuggers. -
 It depends, if you to step through the instructions and put breakpoints, yes you need VMware.
It depends, if you to step through the instructions and put breakpoints, yes you need VMware. -
 If you want to use HyperDbg as a VMI tool, then you can both use HyperDbg in the VMware or without VMware in a physical machine.
If you want to use HyperDbg as a VMI tool, then you can both use HyperDbg in the VMware or without VMware in a physical machine. -
 yeah I need to step through
yeah I need to step through -
 I just can't get user debugging to work
I just can't get user debugging to work -
 Kernel works just fine , just pauses the entire VM though
Kernel works just fine , just pauses the entire VM though -
 In the Debugger Mode (VMware), HyperDbg doesn't care whether you are debugging user mode or kernel mode, all of them are treated the same.
In the Debugger Mode (VMware), HyperDbg doesn't care whether you are debugging user mode or kernel mode, all of them are treated the same. -
 Like you could debug a user mode app, exactly the same as you debug the kernel.
Like you could debug a user mode app, exactly the same as you debug the kernel. -
 E.g., You can run a process using the '.start' command.
E.g., You can run a process using the '.start' command. -
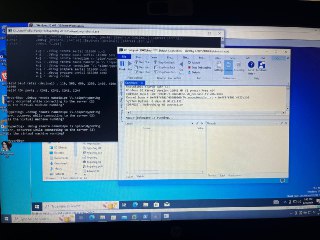
 Ok , so use kdnet.exe on the VM get the host ip address and pick a port, then run the windbg on the host, restart VM, open up hyperdbg-cli and connect via named pipe on the host, go the VM and connect via .debug serial .. right ?
Ok , so use kdnet.exe on the VM get the host ip address and pick a port, then run the windbg on the host, restart VM, open up hyperdbg-cli and connect via named pipe on the host, go the VM and connect via .debug serial .. right ? -
 then open up another hyperdbg-cli and use .start <path_to_exe> or attach PID
then open up another hyperdbg-cli and use .start <path_to_exe> or attach PID -
 Yes. You can see this video too:
Yes. You can see this video too:
https://www.youtube.com/watch?v=MDZ9zYfqo50&ab_channel=OpenSecurityTraining2Dbg3301: HyperDbg 02 04 HyperDbg Lab SetupView the full free MOOC at https://ost2.fyi/Dbg3301. This course is an introductory guide to HyperDbg debugger, guiding you through the initial steps of using HyperDbg, covering essential concepts, principles, debugging functionalities, along with practical examples and numerous reverse engineering methods that are unique to HyperDbg. Whether you have an interest in reverse engineering or seek to elevate your reverse engineering skills with hypervisor-assisted approaches, this course provides a solid foundation for starting your journey.
-
 👍
👍 -
 yeah I'm in the middle of the training , when I have I want to finish it.
yeah I'm in the middle of the training , when I have I want to finish it. -
 Thanks Sina , appreciate your time
Thanks Sina , appreciate your time -

-
 Hmm hyperdbg doesn’t see my vm anymore.
Hmm hyperdbg doesn’t see my vm anymore. -
 Did you run HyperDbg in the VM?
Did you run HyperDbg in the VM? -
 no just the host right now
no just the host right now -
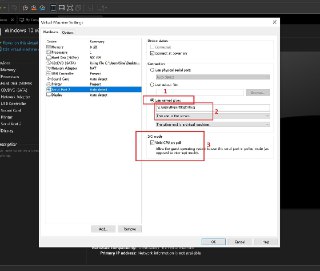
 Is the named pipe (serial) added to the VM?
Is the named pipe (serial) added to the VM? -

-
 Yes
Yes -

-
 Attach to a remote machine | HyperDbg Documentation
Attach to a remote machine | HyperDbg DocumentationRemote debugging in VMI Mode and Debugger Mode
-
 Your configuration is wrong
Your configuration is wrong -
 oh , my bad
oh , my bad - 11 September 2024 (4 messages)
-
 [discord] <ohault> Can you plz update https://docs.hyperdbg.org/getting-started/faq and homepage to specify what are the Windows versions currently supported ?FAQ | HyperDbg Documentation
[discord] <ohault> Can you plz update https://docs.hyperdbg.org/getting-started/faq and homepage to specify what are the Windows versions currently supported ?FAQ | HyperDbg DocumentationFrequently Asked Questions (FAQ)
-
 Generally, HyperDbg supports all versions of Windows (in theory), because HyperDbg doesn't use any special functionality within Windows (most of the things are done by VT-x configurations). But, there might be some incompatibility issues with either SDK or WDK. It's not because HyperDbg doesn't support them, it's because of WDK.
Generally, HyperDbg supports all versions of Windows (in theory), because HyperDbg doesn't use any special functionality within Windows (most of the things are done by VT-x configurations). But, there might be some incompatibility issues with either SDK or WDK. It's not because HyperDbg doesn't support them, it's because of WDK. -
 [discord] <ohault> [reply]: Also old versions of Windows like Windows XP or Windows Server 2003 ?
[discord] <ohault> [reply]: Also old versions of Windows like Windows XP or Windows Server 2003 ? -
 Theoretically, it should work, but I've never tested it, and a modern compiled version of HyperDbg likely won't run on that. However, with Windows 10 is about to be deprecated, why would anyone still use Windows XP 😕🫤
Theoretically, it should work, but I've never tested it, and a modern compiled version of HyperDbg likely won't run on that. However, with Windows 10 is about to be deprecated, why would anyone still use Windows XP 😕🫤 - 12 September 2024 (5 messages)
-
 [discord] <ohault> [reply]: e.g. to debug a very specialised 30 years old industrial software developed by a company in bankruptcy that runs only on Windows XP Embedded
[discord] <ohault> [reply]: e.g. to debug a very specialised 30 years old industrial software developed by a company in bankruptcy that runs only on Windows XP Embedded -
 Joined.
Joined. -
-
 Joined.
Joined. -
- 13 September 2024 (29 messages)
-
 Joined.
Joined. -
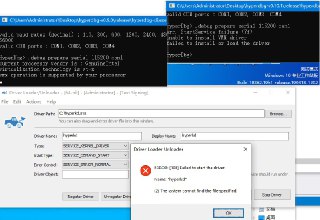
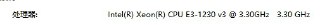
 你好 hyperdbg v0.9可以正常使用,可是 v0.10不能正常载入.."AI translation": Hello, HyperDBG version 0.9 can be used normally, but version 0.10 cannot be loaded properly.
你好 hyperdbg v0.9可以正常使用,可是 v0.10不能正常载入.."AI translation": Hello, HyperDBG version 0.9 can be used normally, but version 0.10 cannot be loaded properly. -
 Hello, HyperDBG version 0.9 can be used normally, but version 0.10 cannot be loaded properly.
Hello, HyperDBG version 0.9 can be used normally, but version 0.10 cannot be loaded properly. -
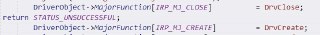
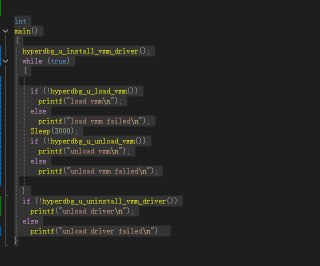
 If I return at the line DriverObject->MajorFunction[IRP_MJ_CLOSE] = DrvClose;, the driver executes normally; otherwise, it throws an error: (2) The system cannot find the file specified.
If I return at the line DriverObject->MajorFunction[IRP_MJ_CLOSE] = DrvClose;, the driver executes normally; otherwise, it throws an error: (2) The system cannot find the file specified. -

-
 我重新测试,发现我错了,v0.10 不工作,v0.9不工作, v0.5工作
我重新测试,发现我错了,v0.10 不工作,v0.9不工作, v0.5工作
I retested and found out I was wrong; v0.10 does not work, v0.9 does not work, v0.5 is work. -
 Usually, these programs can be debugged using old Win XP debuggers.
Usually, these programs can be debugged using old Win XP debuggers. -
 The event will occur but HyperDbg either handle them in the VMX-root mode, sometimes inject them to the target guest debuggee, or completely ignore them as if the event never happens. It depends on the specific event.
The event will occur but HyperDbg either handle them in the VMX-root mode, sometimes inject them to the target guest debuggee, or completely ignore them as if the event never happens. It depends on the specific event. -
 For example, the short-circuiting in the exception command will completely ignore the event as it won't inject it into the OS/APP. So the operating system will not have any idea of such an event even happening.
For example, the short-circuiting in the exception command will completely ignore the event as it won't inject it into the OS/APP. So the operating system will not have any idea of such an event even happening. -
 What about HyperDbg v0.6? Can you tell me exactly which version it stopped working from? I want to check the changelog to see what major changes were introduced in that version, as they might be causing these errors.
What about HyperDbg v0.6? Can you tell me exactly which version it stopped working from? I want to check the changelog to see what major changes were introduced in that version, as they might be causing these errors. -
 Anyway, this processor is very old!!!
Anyway, this processor is very old!!!
It's a Haswell 2013 (4 Gen) processor. I don't really expecting it to work.
https://www.intel.com/content/www/us/en/products/sku/75054/intel-xeon-processor-e31230-v3-8m-cache-3-30-ghz/specifications.html -
 Why are you calling Haswell old? :)
Why are you calling Haswell old? :) -
 Old for what?
Old for what? -
 This is an old processor, 4th generation.
This is an old processor, 4th generation. -
 Not even Win 11 support it.
Not even Win 11 support it. -
 But what’s the problem with the hypervisor?
But what’s the problem with the hypervisor? -
 It doesn't support some of the features of HyperDbg.
It doesn't support some of the features of HyperDbg. -
 I’m just saying it’s not too different in terms of vmx features
I’m just saying it’s not too different in terms of vmx features -
 Which ones?
Which ones? -
 Like we need a post kaby lake (7 gen) processor for our Mode Based Exec Controls (MBEC).
Like we need a post kaby lake (7 gen) processor for our Mode Based Exec Controls (MBEC). -
 Does your hypervisor require that or you’re talking about windows?
Does your hypervisor require that or you’re talking about windows? -
 The hypervisor wants it
The hypervisor wants it -
 Interesting, ok
Interesting, ok -
 We used this feature a lot in a couple of main functionalities of HyperDbg.
We used this feature a lot in a couple of main functionalities of HyperDbg. -
 v0.6 is not working. v0.5 is work,,How can I obtain the error log? Use DbgView?"
v0.6 is not working. v0.5 is work,,How can I obtain the error log? Use DbgView?" -

-
 -----------------------------------------------------
----------------------------------------------------- -

-
 "Are these macro definitions correct?
"Are these macro definitions correct?
#define POOL_FLAG_NON_PAGED 0x0000000000000040UI64 // Non paged pool NX
#define POOL_FLAG_USE_QUOTA 0x0000000000000001UI64 // Charge quota
SDK 10.0.18362.0 does not have these macro definitions. I copied them from GitHub." - 14 September 2024 (4 messages)
-
 Not sure why it's needed
Not sure why it's needed -
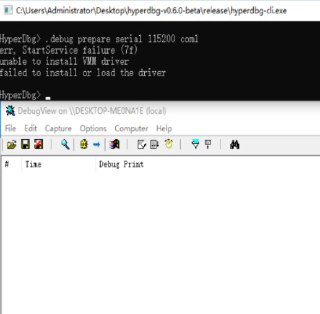
 I see. I suspect to this commit:
I see. I suspect to this commit:
https://github.com/HyperDbg/HyperDbg/commit/bf6370d5a3d35bb7aeb16ce0d45fd77fda7bcca0 -
 Can you check before and after this commit?
Can you check before and after this commit? -
 I think this commit might be the one that breaks the support for your processor (within v0.5 to v0.6).
I think this commit might be the one that breaks the support for your processor (within v0.5 to v0.6). - 15 September 2024 (11 messages)
-
 你好,我可能知道是什么原因了,应该是引入了旧版windows不兼容的api导致的,,我在40c9f5a没有编译错误,在16ab766出现编译错误,我关闭了Visual Studio 2022->hyperkd Property Page->ApiValidator->Run ApiValidator之后可以编译,但是windows1903拒绝加载它
你好,我可能知道是什么原因了,应该是引入了旧版windows不兼容的api导致的,,我在40c9f5a没有编译错误,在16ab766出现编译错误,我关闭了Visual Studio 2022->hyperkd Property Page->ApiValidator->Run ApiValidator之后可以编译,但是windows1903拒绝加载它 -
 Hello, I might know what the reason is. It seems that an API that is not compatible with older versions of Windows was introduced. I don't have compilation errors at commit 40c9f5a, but I encounter compilation errors at commit 16ab766. After I turned off the "Run ApiValidator" option in Visual Studio 2022 under the hyperkd Property Page -> ApiValidator, I was able to compile, but Windows 1903 refuses to load it.
Hello, I might know what the reason is. It seems that an API that is not compatible with older versions of Windows was introduced. I don't have compilation errors at commit 40c9f5a, but I encounter compilation errors at commit 16ab766. After I turned off the "Run ApiValidator" option in Visual Studio 2022 under the hyperkd Property Page -> ApiValidator, I was able to compile, but Windows 1903 refuses to load it. -

-

-

-

-
 Validating Windows Drivers - Windows drivers
Validating Windows Drivers - Windows driversVarious tools to use to validate that your driver package is compliant with the Windows Drivers rules.
-

-

-
 40c9f5a is working
40c9f5a is working -
 16db766 is no working
16db766 is no working - 16 September 2024 (1 messages)
-
Joined.
- 17 September 2024 (4 messages)
-
 Nothing special changed in this commit, it's just bringing all allocation functions into a unified function. 🤔
Nothing special changed in this commit, it's just bringing all allocation functions into a unified function. 🤔 -
I guess the problem from ExAllocatePool
-
Updating Deprecated ExAllocatePool Calls to ExAllocatePool2 and ExAllocatePool3 - Windows drivers
Learn about Updating deprecated ExAllocatePool calls to ExAllocatePool2 and ExAllocatePool3
-
for old WDK version, you can try to replace ExAllocatePool2 to ExAllocatePool
- 18 September 2024 (1 messages)
-
 Joined.
Joined. - 21 September 2024 (6 messages)
-
-
 In VMI mode?
In VMI mode? -
debugger
-
-
-
 Based on our previous group discussions, it seems that the physical serial connection is not working properly. We've tried several times to port kdnet to HyperDbg but, unfortunately, have not succeeded yet. For now, only VMI Mode is available for a physical machine.
Based on our previous group discussions, it seems that the physical serial connection is not working properly. We've tried several times to port kdnet to HyperDbg but, unfortunately, have not succeeded yet. For now, only VMI Mode is available for a physical machine. - 23 September 2024 (1 messages)
-
Joined.
- 25 September 2024 (1 messages)
-
Joined.
- 27 September 2024 (1 messages)
-
 Joined.
Joined. - 28 September 2024 (16 messages)
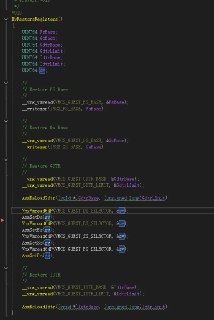
-

-

-

-

-

-

-
 Not sure if I understand it correctly. Can you explain the scenario where this error might happen?
Not sure if I understand it correctly. Can you explain the scenario where this error might happen?
I assume you're trying to unload HyperDbg while it's in the middle of running a user-mode application? -

-

-

-

-

-

-
 And this change in setting segment selectors fix the issue?
And this change in setting segment selectors fix the issue? -
 Thanks for reporting it, I'll try to reproduce it.
Thanks for reporting it, I'll try to reproduce it. -
 If yes, pls make sure to send a Pull Request to the HyperDbg repo (the 'dev' branch) to fix it.
If yes, pls make sure to send a Pull Request to the HyperDbg repo (the 'dev' branch) to fix it. - 29 September 2024 (10 messages)
-

-

-
-
 You mean conditional stepping?
You mean conditional stepping? -
using the "i 10000" command, set a condition for checking the register, for example if @rip < 0x... then....
-
 It's actually possible but I'm not sure if I export it properly for the regular usage. But, in case if you can compile HyperDbg's libhyperdbg, you need to check for your condition in the C code and recompile. It should be super easy.
It's actually possible but I'm not sure if I export it properly for the regular usage. But, in case if you can compile HyperDbg's libhyperdbg, you need to check for your condition in the C code and recompile. It should be super easy. -
 This is the function responsible for sending instrumentation step-in requests:
This is the function responsible for sending instrumentation step-in requests:
https://github.com/HyperDbg/HyperDbg/blob/38f7e747d688846c0d82e299338b66d7730e4559/hyperdbg/libhyperdbg/code/debugger/core/steppings.cpp#L26HyperDbg/hyperdbg/libhyperdbg/code/debugger/core/steppings.cpp at 38f7e747d688846c0d82e299338b66d7730e4559 · HyperDbg/HyperDbgState-of-the-art native debugging tools. Contribute to HyperDbg/HyperDbg development by creating an account on GitHub.
-
 And this is where a Cpp code gets called when you step one instructions:
And this is where a Cpp code gets called when you step one instructions:
https://github.com/HyperDbg/HyperDbg/blob/38f7e747d688846c0d82e299338b66d7730e4559/hyperdbg/libhyperdbg/code/debugger/kernel-level/kernel-listening.cpp#L361
Add your condition here. ☝️HyperDbg/hyperdbg/libhyperdbg/code/debugger/kernel-level/kernel-listening.cpp at 38f7e747d688846c0d82e299338b66d7730e4559 · HyperDbg/HyperDbgState-of-the-art native debugging tools. Contribute to HyperDbg/HyperDbg development by creating an account on GitHub.
-
that is, to set the condition directly from the C code?
-
 Yes
Yes - 30 September 2024 (1 messages)
-
Joined.
- 01 Sep 2024 (55)
- 03 Sep 2024 (11)
- 04 Sep 2024 (8)
- 05 Sep 2024 (32)
- 06 Sep 2024 (3)
- 08 Sep 2024 (11)
- 09 Sep 2024 (1)
- 10 Sep 2024 (47)
- 11 Sep 2024 (4)
- 12 Sep 2024 (5)
- 13 Sep 2024 (29)
- 14 Sep 2024 (4)
- 15 Sep 2024 (11)
- 16 Sep 2024 (1)
- 17 Sep 2024 (4)
- 18 Sep 2024 (1)
- 21 Sep 2024 (6)
- 23 Sep 2024 (1)
- 25 Sep 2024 (1)
- 27 Sep 2024 (1)
- 28 Sep 2024 (16)
- 29 Sep 2024 (10)
- 30 Sep 2024 (1)