- 01 January 2026 (4 messages)
-
Happy new year, wish everyone a great year ahead
-

-
-
Joined.
- 02 January 2026 (1 messages)
-
 Joined.
Joined. - 05 January 2026 (6 messages)
-
 Joined.
Joined. -
Joined.
-

-

-
 PVOID
PVOID
ExAllocatePoolWithTagHook(
POOL_TYPE PoolType,
SIZE_T NumberOfBytes,
ULONG Tag)
{
LogInfo("ExAllocatePoolWithTag Called with : Tag = 0x%x, Number Of Bytes = 0x%x, Pool Type = 0x%x ",
Tag,
NumberOfBytes,
PoolType);
return ExAllocatePoolWithTagOrig(PoolType, NumberOfBytes, Tag);
} -

- 07 January 2026 (7 messages)
-
 Unknown or unsupported property value '1.9' for KmdfVersion for target OS 'Windows10' (0x0601). [D:\HyperDbg\hyperdbg\dependencies\zydis\msvc\zydis\Zydis.vcxproj]
Unknown or unsupported property value '1.9' for KmdfVersion for target OS 'Windows10' (0x0601). [D:\HyperDbg\hyperdbg\dependencies\zydis\msvc\zydis\Zydis.vcxproj] -
 Does anyone know how to fix this error?
Does anyone know how to fix this error? -
 Hey,
Hey,
You shouldn't use this example. It is old and I don't think that it works anymore. -
 If you want to use the classic/detour EPT hook, follow hyperkd.sys's "Debugger.c" routines to see how we called !epthook.
If you want to use the classic/detour EPT hook, follow hyperkd.sys's "Debugger.c" routines to see how we called !epthook. -
 @koksdk
@koksdk
This is the function that you need to call to put EPT hooks: https://github.com/HyperDbg/HyperDbg/blob/5462d69dd189cdfca3a889daca3fb6eb8abf080d/hyperdbg/hyperkd/code/debugger/events/ApplyEvents.c#L324HyperDbg/hyperdbg/hyperkd/code/debugger/events/ApplyEvents.c at 5462d69dd189cdfca3a889daca3fb6eb8abf080d · HyperDbg/HyperDbgState-of-the-art native debugging tools. Contribute to HyperDbg/HyperDbg development by creating an account on GitHub.
-
 Hey
Hey
This is the problem of new SDK with zydis. -
 @mojtabafaaleh
@mojtabafaaleh
use this solution. - 08 January 2026 (2 messages)
-
 Tnx ❤️❤️❤️
Tnx ❤️❤️❤️ -
 Joined.
Joined. - 12 January 2026 (2 messages)
-
 Thanks❤️
Thanks❤️ -
Joined.
- 16 January 2026 (1 messages)
-

- 21 January 2026 (21 messages)
-
Does anyone have a hyper that can bypass CR3?
-
I would like to separate it out as a standalone entity.
-
 What do you mean by that?
What do you mean by that? -
That is, there’s no need to use hyperdbg.
-
But wanting to use it
-
I would like to bypass the CR3 check.
-
 Where does this check come from? Please provide more context
Where does this check come from? Please provide more context -
The process itself includes integrity checks.
-
So I’m unable to modify that code snippet.
-
 PulseDbg of mine is an isolated hypervisor. It is not open source, but it has SDK. It also requires two physical machines for debugging. Don't know if it helps in your situation.\
PulseDbg of mine is an isolated hypervisor. It is not open source, but it has SDK. It also requires two physical machines for debugging. Don't know if it helps in your situation.\ -
Is it an open-source program? I can give it a try.
-
Yes, I need a hypervisor.
-
I want to create a crack patch.
-
However, the program itself includes a CR3 check.
-
Therefore, I would like to use a hypervisor to make these modifications without leaving any traces.
-
 Sorry, we don't discuss cracks or harmful patches here
Sorry, we don't discuss cracks or harmful patches here -
Lol, what I cracked was a Trojan program.
-
So this is legal, bro.
-
 Okay, gotcha!
Okay, gotcha! -
 Feel free to DM me with further questions about pulsedbg then
Feel free to DM me with further questions about pulsedbg then -
 hello there can I have a list of resources to learn how hypervisors work and how to develop them?
hello there can I have a list of resources to learn how hypervisors work and how to develop them? - 22 January 2026 (2 messages)
-
me too
-
 This might be helpful:
This might be helpful:
https://github.com/Wenzel/awesome-virtualizationGitHub - Wenzel/awesome-virtualization: Collection of resources about VirtualizationCollection of resources about Virtualization. Contribute to Wenzel/awesome-virtualization development by creating an account on GitHub.
- 24 January 2026 (4 messages)
-
 when are you going to publish the 9th part of your series hypervisor from scratch?
when are you going to publish the 9th part of your series hypervisor from scratch? -
 Well, writing a new hypervisor from scratch requires at least three months of dedicated research and development. Given my current obligations, I can't devote that much time at the moment. However, I hope my schedule becomes less busy in the future so I can write another one.
Well, writing a new hypervisor from scratch requires at least three months of dedicated research and development. Given my current obligations, I can't devote that much time at the moment. However, I hope my schedule becomes less busy in the future so I can write another one. -
 what prior knowledge do I need to develop hypervisors?
what prior knowledge do I need to develop hypervisors? -
 you could check out intel IA-32
you could check out intel IA-32 - 25 January 2026 (5 messages)
-
is amd harder to dive in ?
-
 the hypervisors i saw were all intel vt-x based 😂 i dont know much about AMD there might be less resources
the hypervisors i saw were all intel vt-x based 😂 i dont know much about AMD there might be less resources -
 C/C++ ( atleast 3 - 5 year experience )
C/C++ ( atleast 3 - 5 year experience )
ASM
IA-32 -
This might be helpful:
https://github.com/Wenzel/awesome-virtualizationGitHub - Wenzel/awesome-virtualization: Collection of resources about VirtualizationCollection of resources about Virtualization. Contribute to Wenzel/awesome-virtualization development by creating an account on GitHub.
-
This is a good tutorial; I hope I can use it to implement hyper.
- 26 January 2026 (1 messages)
-
- 27 January 2026 (27 messages)
-
 [discord] <r3d_malz> Hi ! I was trying to write into discussion channel from Github but maybe its disable.
[discord] <r3d_malz> Hi ! I was trying to write into discussion channel from Github but maybe its disable.
I am new into HyperDbg and I wanted to know few things before dive in:
- If I want to debug a guest VM (Vmware/Hyper-V...) is Intel proc mandatory ?
- Is it easier to debug the boot steps and see hvix64 in the dbg ? -
 Hi!
Hi!
- Yes, it's an Intel-only hypervisor. AMD has a different implementation of virtualization extension.
- As far as I understand hvix64 starts way before hyperdbg. Hyperdbg might have a problem with nested VMX as well. hvix64 is also a hypervisor (btw Intel based, hvax64 is AMD based) -
 The two methods for debugging hvix64 are the built-in kernel debugger (hypervisordebug in bcd) and JTAG
The two methods for debugging hvix64 are the built-in kernel debugger (hypervisordebug in bcd) and JTAG -
 *that I'm aware of
*that I'm aware of -
 [discord] <r3d_malz> Ooooh.. I was using a setup like host(W11)->wmware(W11) using bcedit and windbg on my host. I successfully break into hv but break the vm after that :/
[discord] <r3d_malz> Ooooh.. I was using a setup like host(W11)->wmware(W11) using bcedit and windbg on my host. I successfully break into hv but break the vm after that :/
Let's buy an intel pc ... -
 Buying a physical machine for debugging is always a safer bet :)
Buying a physical machine for debugging is always a safer bet :) -
 [discord] <r3d_malz> don't have ressources on the hardware to buy for the moment but I think you're 100% right haha
[discord] <r3d_malz> don't have ressources on the hardware to buy for the moment but I think you're 100% right haha
I try 5 method to debug kernel/hv/securekernel and everything is broken (maybe a bit of skill issue) -
 I would bet it's vmware. It has to support nested vmx for enabling hvix. Nested hypervisors are hard, even for vmware. I don't even blame them.
I would bet it's vmware. It has to support nested vmx for enabling hvix. Nested hypervisors are hard, even for vmware. I don't even blame them. -
 Anyone knows why MmGetVirtualForPhysical fails for certain addresses?
Anyone knows why MmGetVirtualForPhysical fails for certain addresses? -
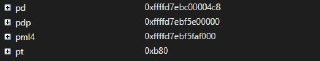
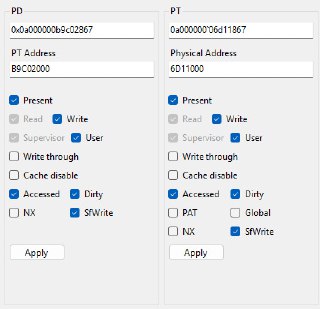
 I'm somehow always getting 0xb80 while traversing page tables on PT
I'm somehow always getting 0xb80 while traversing page tables on PT -
 No. It's much more clear and you have an (actual) structure instead of weird vmwrite and vmreads. There are less implementations and references, though.
No. It's much more clear and you have an (actual) structure instead of weird vmwrite and vmreads. There are less implementations and references, though. -
 And my values are fine.
And my values are fine. -
 MSDN: The MmGetPhysicalAddress routine returns the physical address corresponding to a valid nonpaged virtual address.
MSDN: The MmGetPhysicalAddress routine returns the physical address corresponding to a valid nonpaged virtual address. -
 So the question is
So the question is -
 Is it a valid non paged address?
Is it a valid non paged address? -
 It's MmGetVirtualForPhysical. Not MmGetPhysicalAddress
It's MmGetVirtualForPhysical. Not MmGetPhysicalAddress -
 My bad
My bad -
 And yes. ExAllocatePool2
And yes. ExAllocatePool2 -
 It's not documented, however its in wdk headers
It's not documented, however its in wdk headers -
 "Does not search the page tables. It relies on the internal implementation detail that the low part of the kernel virtual space is mapped 1:1 into physical space at a known location. All it does is a little masking and arithmetic on the address. It doesn’t use the page tables, and it won’t find any user-mode mappings."
"Does not search the page tables. It relies on the internal implementation detail that the low part of the kernel virtual space is mapped 1:1 into physical space at a known location. All it does is a little masking and arithmetic on the address. It doesn’t use the page tables, and it won’t find any user-mode mappings."
I think it fails on my allocation. But sometimes it doesn't? It sometimes works, sometimes doesn't while mapping on the same address. -
 I'm not sure I get what you're doing. Do you allocate a non-paged pool chunk with ExAllocatePool2, then get its physical memory and then use MmGetVirtualForPhysical to get the virtual address again?
I'm not sure I get what you're doing. Do you allocate a non-paged pool chunk with ExAllocatePool2, then get its physical memory and then use MmGetVirtualForPhysical to get the virtual address again? -
 I checked MmGetVirtualForPhysical function in IDA and it seems to me that it was designed for page table lookups. Like when you have a CR3 value (which is a physical address) and you want to get a virtual address for it to be able to use it with a CPU thread.
I checked MmGetVirtualForPhysical function in IDA and it seems to me that it was designed for page table lookups. Like when you have a CR3 value (which is a physical address) and you want to get a virtual address for it to be able to use it with a CPU thread.
Anyways, it is deprecated. No wonder it is not documented. You would generally avoid using undocumented functions for this exact reason - noone guarantees it will work forever. -
 Yes. That's correct.
Yes. That's correct. -
 What else chance I have?
What else chance I have? -
 Depends on what problem you are solving. What is your scenario>
Depends on what problem you are solving. What is your scenario> -
 I'm trying to create my own mappings. So I have to get virtual adresses of page entries, to modify them
I'm trying to create my own mappings. So I have to get virtual adresses of page entries, to modify them -
 [discord] <axaxaaxaxaaxa> [reply]: nah it works fine with vmwares gdb stub
[discord] <axaxaaxaxaaxa> [reply]: nah it works fine with vmwares gdb stub - 30 January 2026 (1 messages)
-
 Curious about anti-anti-debugging techniques and hiding hypervisors from malware? Or simply looking for an in-depth introduction to @HyperDbg? Join our FOSDEM talks presented by [Sina Karvandi] and [Björn Ruytenberg] tomorrow:
Curious about anti-anti-debugging techniques and hiding hypervisors from malware? Or simply looking for an in-depth introduction to @HyperDbg? Join our FOSDEM talks presented by [Sina Karvandi] and [Björn Ruytenberg] tomorrow:
https://fosdem.org/2026/schedule/event/APB9WC-mbec_slat_and_hyperdbg_hypervisor-based_kernel-_and_user-mode_debugging/
https://fosdem.org/2026/schedule/event/CDPRDX-invisible_hypervisors_debugging_with_hyperdbg/ - 31 January 2026 (3 messages)
-
 We brought plenty of HyperDbg stickers to give away at FOSDEM! Find us after our talks or ping us to grab yours.
We brought plenty of HyperDbg stickers to give away at FOSDEM! Find us after our talks or ping us to grab yours.
- Security track: Room UB5.132 (13:00-13:25)
- Virtualization track: Room H.2213 (18:30-19:00)
#FOSDEM2026 #FOSDEM #HyperDbg -
Are the slides gonna be available later?
-